What is Apollon865 ransomware? And how does it execute its attack?
Apollon865 ransomware is a file-encrypting virus discovered recently. According to security researchers, it is a new variant of GlobeImposter ransomware. It attaches a “.Apollon865” extension to every file it corrupts and the moment it invades a targeted computer, it will connect to its remote Command and Control server where it downloads more malicious files and drops them into the system. It also makes changes in the Windows Registry so it can run every time users boot their PCs. After that, it will look for the following file types and begin encrypting important data.
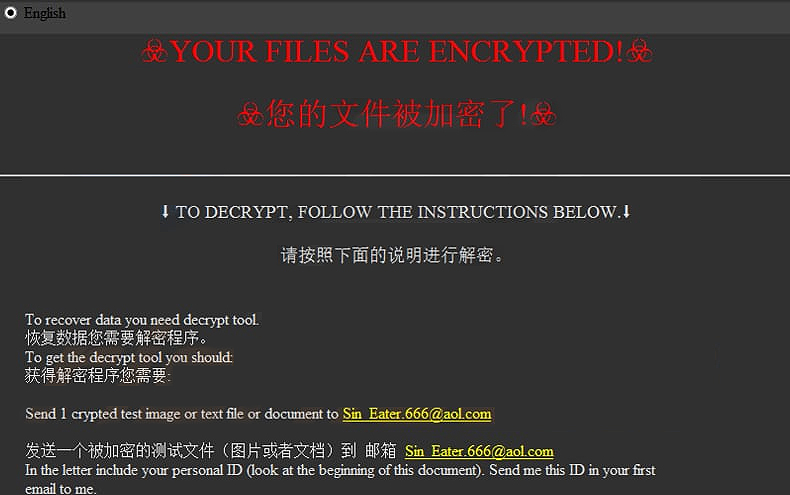
“Your personal ID
–
English ☣Your files are encrypted!☣
☣您的文件被加密了!☣
————————
⬇ To decrypt, follow the instructions below.⬇
请按照下面的说明进行解密。
To recover data you need decrypt tool.
恢复数据您需要解密程序。
To get the decrypt tool you should:
获得解密程序您需要:
Send 1 crypted test image or text file or document to [email protected]
发送一个被加密的测试文件(图片或者文档)到 邮箱 [email protected]
In the letter include your personal ID (look at the beginning of this document). Send me this ID in your first email to me.
We will give you free test for decrypt few files (NOT VALUE) and assign the price for decryption all files.
After we send you instruction how to pay for decrypt tool and after payment you will receive a decrypt tool and instructions how to use it We can decrypt few files in quality the evidence that we have the decoder.
邮件内容需要包含您的个人ID(请看文档开始的ID)。
我们将会解密测试文件并给出解密全部文件的价格。
然后我们会告诉您如何购买解密程序,支付解密费用后您将收到解密程序和使用说明。 我们解密一个文件是为了证明我们拥有解码器.
————————
MOST IMPORTANT!!!
非常重要!!!
Do not contact other services that promise to decrypt your files, this is fraud on their part! They will buy a decoder from us, and you will pay more for his services. No one, except [email protected], will decrypt your files.
不要联系其他保证能解密您文件的人,他们是在欺骗您! 他们需要从我们这里购买解码器,而且您需要为此支付更多的费用。”
How does Apollon865 ransomware proliferate?
Apollon865 ransomware proliferates via spam emails containing an infected attachment or corrupted link. Crooks mostly attach infected files in emails containing malicious scripts used to install crypto-malware like Apollon865 ransomware in the system. This is why you need to double-check the email first before you download and open the attached file as it could be a harmful one that could cause damage to your computer.
Obliterating Apollon865 ransomware from your computer wouldn’t be that easy so you need to follow the removal guide provided below.
Step_1: The first thing you need to do is to obliterate the process of Apollon865 ransomware by opening the Task Manager – simply tap the Ctrl + Shift + Esc keys on your keyboard.
Step_2: After that, switch to the Processes tab and look for a process named HOW TO BACK YOUR FILES.exe as well as any suspicious-looking process that takes up most of your CPU’s resources and is most likely related to Apollon865 ransomware, and then end them all.
Step_3: Now that the malicious processes are eliminated, close the Task Manager.
Step_4: Next, tap Win + R, type in appwiz.cpl and click OK or tap Enter to open Control Panel’s list of installed programs.
Step_5: Under the list of installed programs, look for Apollon865 ransomware or anything similar, and then uninstall it.
Step_6: Then close Control Panel and tap Win + E keys to launch File Explorer.
Step_7: Navigate to the following locations below and look for the malicious components of Apollon865 ransomware like the file named HOW TO BACK YOUR FILES.exe, and [random].exe, as well as other suspicious files it has created and downloaded into the system, and then delete all of them.
- %LOCALAPPDATA%
- %APPDATA%
- %TEMP%
- %WINDIR%\System32\Tasks
- %APPDATA%\Microsoft\Windows\Templates\
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
Step_8: Close the File Explorer.
Before you go on any further, make sure that you are tech-savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use Restoro this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step_9: Tap Win + R to open Run and then type in Regedit in the field and tap enter to pull up Windows Registry.
Step_10: Navigate to the following path:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step_11: Delete the registry keys and sub-keys created by Apollon865 ransomware.
Step_12. Close the Registry Editor and empty the Recycle Bin.
Try to recover your encrypted files using the Shadow Volume copies
Restoring your encrypted files using Windows Previous Versions feature will only be effective if Apollon865 ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.
Congratulations, you have just removed Apollon865 Ransomware in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
Now that’s how you remove Apollon865 Ransomware in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
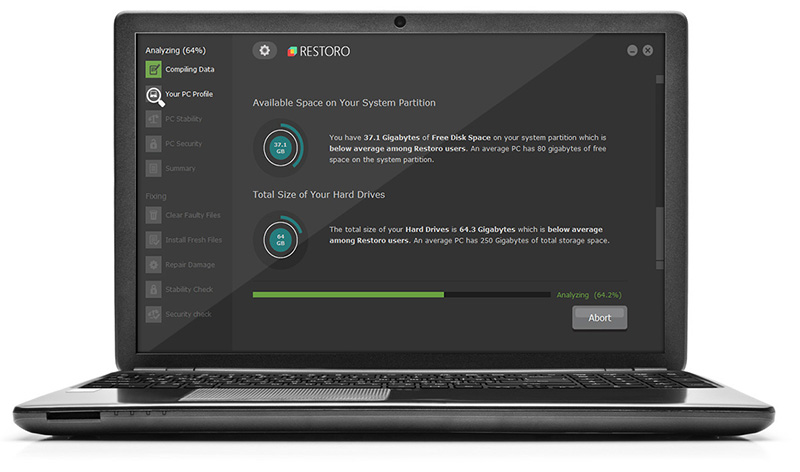
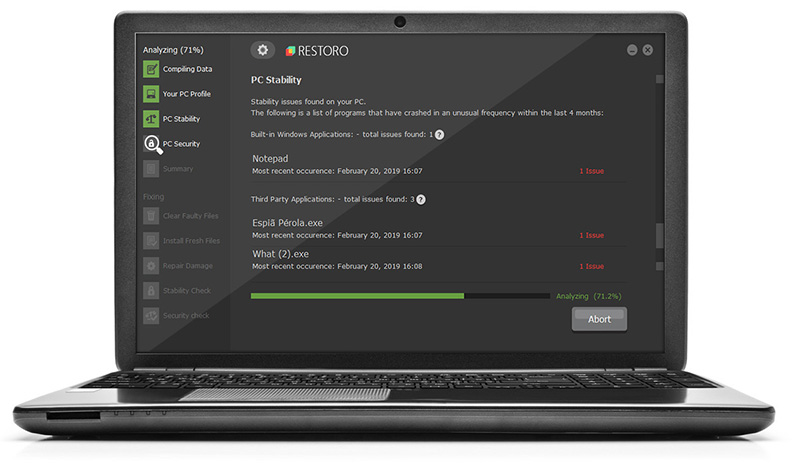
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.