What is Muhstik ransomware? And how does it execute its attack?
Muhstik ransomware is one of the ransomware threats discovered in early October 2019. This new crypto-malware was seen targeting NAS devices by using brute force via the devices’ security flaws and weak passwords. According to security researchers, it is a new variant of eCh0raix ransomware.
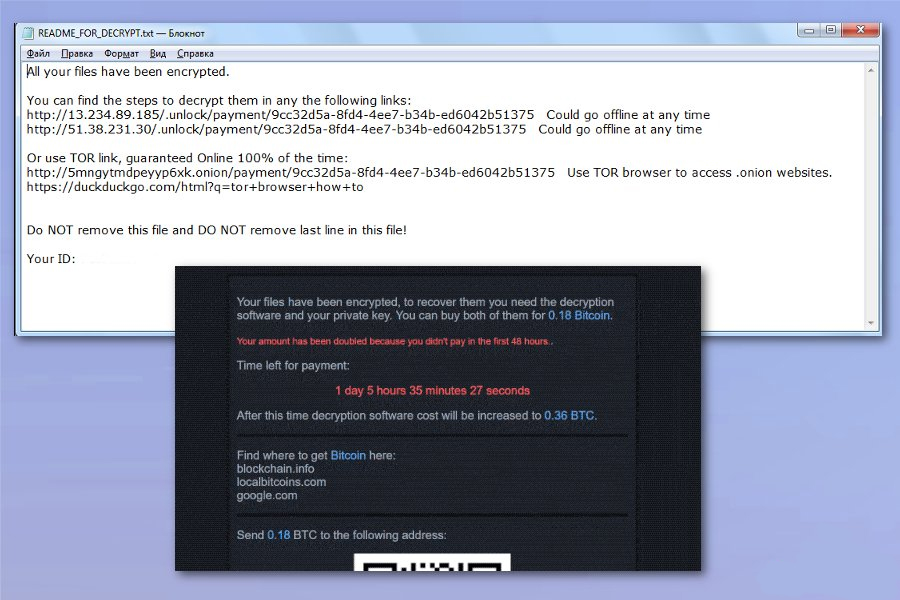
The instant Mushtik ransomware infiltrates a targeted device, it gains access to the phpMyAdmin installation and executes its payload file in the system. Following the infiltration, this crypto-malware checks if the system language is in Russian, Belarus, or Ukraine, and if it finds that the computer is from any of the aforementioned countries, it does not encrypt the files in the system. However, if the infected computer is not from any of these countries, it encrypts the important data in the system. It then begins the encryption process using a sophisticated encryption algorithm and adds the “.muhstik” extension to every file affected. Once the encryption is completed, it delivers its ransom note named “README_FOR_DECRYPT.txt” which contains the following message:
“All your files have been encrypted.
You can find the steps to decrypt in any of the following links:
hxxp://13.234.89.185/.unlock/payment/[victim’s_ID] Could go offline at any time
hxxp://51.38.231.30/.unlock/payment/[victim’s_ID] Could go offline at any time
Or use TOR link, guaranteed Online 100% of the time:
hxxp://5mngytmdpeyyp6xk.onion/payment/[victim’s_ID] Use TOR browser to access .onion websites.
hxxps://duckduckgo.com/html?q=tor+browser+how+to
Do NOT remove this file and DO NOT remove the last line in this file!
Your ID:”
Moreover, Muhstik ransomware also redirects users to a website that contains instructions on how to pay the ransom. The site contains the following content:
“Your files have been encrypted, to recover them you need the decryption software and your private key. You can buy both of them for 0.045 Bitcoin.
Time left for payment:
1 day 17 hours 4 minutes 14 seconds
After this time decryption software cost will be increased to 0.09 BTC.
Find where to get Bitcoin here:
blockchain.info
localbitcoins.com
google.com
Send 0.045 BTC to the following address:
133Y64UxdzREJqYjxXxR3qebbgafpq5FG1
ONLY SUBMIT YOUR EMAIL AFTER YOU SENT THE BTC.
If you submit your email before sending the payment your amount will be instantly doubled!
After payment enters your real email address to get the decryptor software.
Enter a valid email address
Your decrypted demo file is ready to download, open the following link.
http://13.233.53.172/.cache/download/9cc32d5a-8fd4-4ee7-b34b-ed6042b51375-split-IMG_20160608_111553.jpg”
How does Muhstik ransomware spread online?
Like pointed out, Muhstik ransomware infects a computer by using brute force. Aside from that, it may also spread via malicious spam email campaigns just like its predecessors. Attackers mostly attached an infected file to spam emails. The infected file may be a document with malicious macro scripts used to install Muhstik ransomware in the targeted machine. This is why you need to be more cautious in downloading attachments from emails no matter who the sender is as crooks tend to disguise these malware-laden emails to trick users into opening them and downloading the infected attachment.
With the help of the removal guide prepared, obliterate Muhstik ransomware and its malicious components from the infected computer.
Step_1: First, restart your PC and boot into Safe Mode with Command Prompt by tapping F8 a couple of times until the Advanced Options menu appears.
Step_2: Next, navigate to Safe Mode with Command Prompt using the arrow keys on your keyboard. After selecting Safe Mode with Command Prompt, hit Enter.
Step_3: After loading the Command Prompt type cd restore and hit Enter.
Step_4: After cd restore, type in rstrui.exe and hit Enter.
Step_5: A new window will appear, and then click Next.
Step_6: Select any of the Restore Points on the list and click Next. This will restore your computer to its previous state before being infected with the Muhstik Ransomware. A dialog box will appear and then click Yes.
Step_7: After System Restore has been completed, try to enable the disabled Windows services.
- Press Win + R keys to launch Run.
- Type in gpedit.msc in the box and press Enter to open Group Policy.
- Under Group Policy, navigate to:
- User Configuration\Administrative Templates\System
- After that, open Prevent access to the command prompt.
- Select Disable to enable cmd
- Click the OK button
- After that, go to:
- Configuration\Administrative Templates\System
- Double click on the Prevent Access to registry editing tools.
- Choose Disabled and click OK.
- Navigate to :
- User Configuration\Administrative Templates\System>Ctrl+Alt+Del Options
- Double click on Remove Task Manager.
- And then set its value to Disabled.
Step_8: Next, tap Ctrl + Shift + Esc to open the Task Manager and then go to the Processes tab and look for the malicious processes of Muhstik Ransomware and end them all.
Step_9: Open Control Panel by pressing Start key + R to launch Run and type appwiz.cpl in the search box and click OK to open the list of installed programs. From there, look for Muhstik ransomware or any malicious program and then Uninstall it.
Step_10: Tap Windows + E keys to open the File Explorer then navigate to the following directories and delete the malicious files created by Muhstik ransomware such as README_FOR_DECRYPT.txt and [random].exe.
- %UserProfile%\AppData
- %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup
- %TEMP%.
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
Step_11: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech-savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you trouble and time, you can just use Restoro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step_12: Tap Win + R to open Run and then type in Regedit in the field and tap enter to pull up Windows Registry.
Step_13: Navigate to the paths listed below and delete all the registry values added by Muhstik ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step_14: Close the Registry Editor and empty your Recycle Bin.
Try to recover your encrypted files using their Shadow Volume copies
Restoring your encrypted files using Windows Previous Versions feature will only be effective if Muhstik ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.
Congratulations, you have just removed Muhstik Ransomware in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
Now that’s how you remove Muhstik Ransomware in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
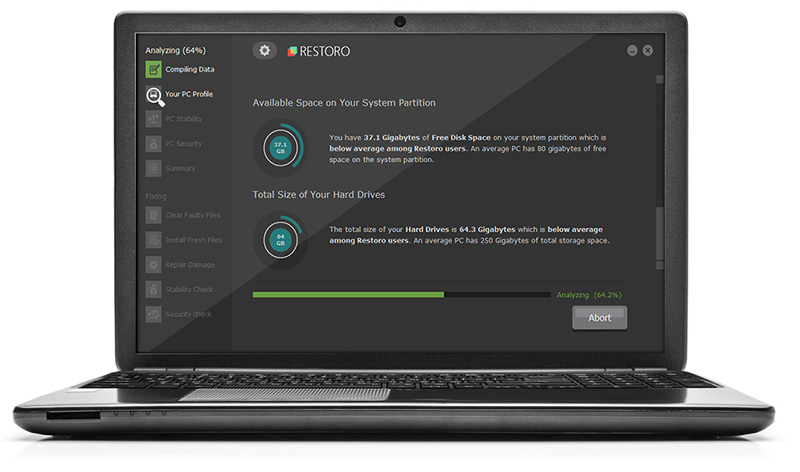
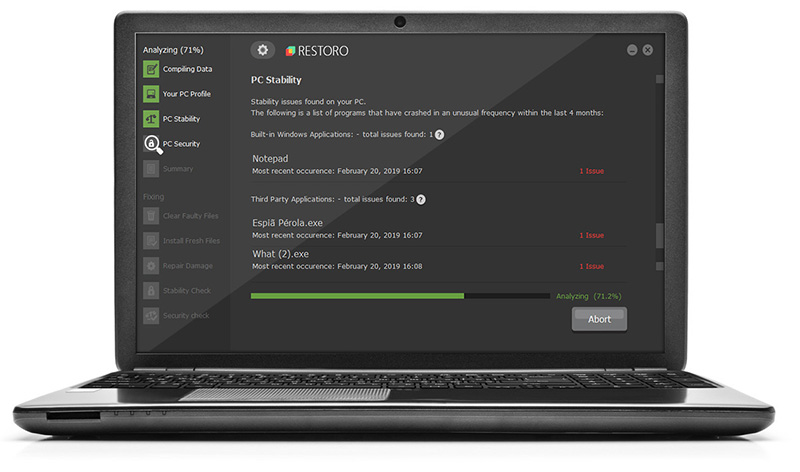
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.