What is VegaLocker ransomware? And how does it implement its attack?
VegaLocker ransomware is one of the crypto-viruses discovered in early February 2019. Based on its code analysis, it was found that this new crypto-virus is programmed using the Delphi programming language. It also contains code snippets from the infamous Scarab ransomware. What’s more is that its source code also includes snippets from Amnesia, Gloverabe2, and other ransomware threats.
According to security experts, creators of this ransomware threat seem to have taken the source code of several ransomware groups and created the custom code by themselves. This means that VegaLocker ransomware is the result of combined ransomware threats. This cryptovirus also includes signatures from various products, services, and companies which makes it very convenient to use with infected applications. VegaLocker ransomware also features a stealth protection module that can bypass security software in the computer such as antivirus software, firewalls, debug environments, machine hosts, and so on.
After it infiltrates a computer, VegaLocker ransomware will implement a series of scripts that will disable access to the boot recovery options which will make its removal even harder than it already is. Another dangerous trait of this ransomware is that it’s been programmed specifically to evade virtual machine hosts. It will scan the memory and locate any strings related to hypervisors as well as utility software and drivers that can reveal that the host is actually part of a virtual machine installation. Thus, when it’s detected, VegaLocker ransomware will stop its attack or will simply delete itself to avoid detection.
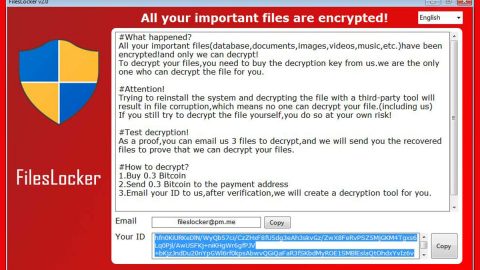
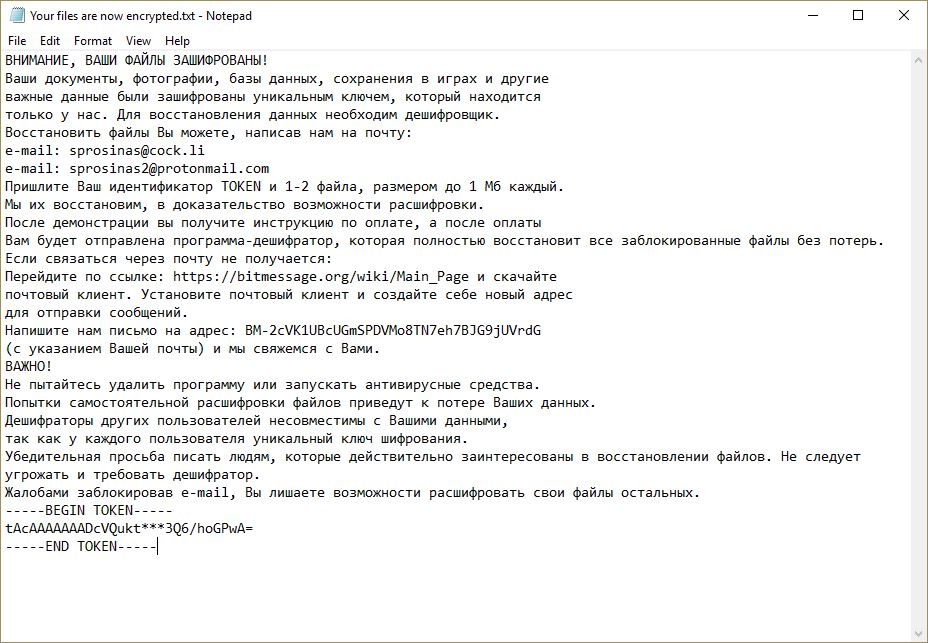
In addition, it is also found to modify the Desktop.rdp configuration file which is used to configure remote desktop sessions. Once it’s done carrying out system modifications, it starts the encryption using the AES cipher. It does not add any extension to the files it encrypts and only opens a ransom note named “Your files are now encrypted.txt” which contains the following message:
“ВНИМАНИЕ, ВАШИ ФАЙЛЫ ЗАШИФРОВАНЫ!
Ваши документы, фотографии, базы данных, сохранения в играх и другие
важные данные были зашифрованы уникальным ключем, который находится
только у нас. Для восстановления данных необходим дешифровщик.
Восстановить файлы Вы можете, написав нам на почту:
e-mail: [email protected]
e-mail: [email protected]
Пришлите Ваш идентификатор TOKEN и 1-2 файла, размером до 1 Мб каждый.
Мы их восстановим, в доказательство возможности расшифровки.
После демонстрации вы получите инструкцию по оплате, а после оплаты
Вам будет отправлена программа-дешифратор, которая полностью восстановит все заблокированные файлы без потерь.
Если связаться через почту не получается:
Перейдите по ссылке: https://bitmessage.org/wiki/Main_Page и скачайте
почтовый клиент. Установите почтовый клиент и создайте себе новый адрес
для отправки сообщений.
Напишите нам письмо на адрес: BM-2cVK1UBcUGmSPDVMo8TN7eh7BJG9jUVrdG
(с указанием Вашей почты) и мы свяжемся с Вами.
ВАЖНО!
Не пытайтесь удалить программу или запускать антивирусные средства.
Попытки самостоятельной расшифровки файлов приведут к потере Ваших данных.
Дешифраторы других пользователей несовместимы с Вашими данными,
так как у каждого пользователя уникальный ключ шифрования.
Убедительная просьба писать людям, которые действительно заинтересованы в восстановлении файлов. Не следует угрожать и требовать дешифратор.
Жалобами заблокировав e-mail, Вы лишаете возможности расшифровать свои файлы остальных.
—–BEGIN TOKEN—–
tAcAAAAAAADcVQukt***3Q6/hoGPwA=
—–END TOKEN—–”
How does VegaLocker ransomware proliferate?
Based on the captured samples of VegaLocker ransomware, it is found to use the following signatures in spreading the web:
Habbo, Rebhip, The Qt Company Ltd, Microsoft Corporation, Delphi Libraries, SMART INSTALL MAKER, InnoSetup, James Jackson-South, Microsoft Visual C/C++ Libraries, libczmq3, Adobe Systems Incorporated, Mercury Interactive, NSIS, Splinterware Software Solutions, and StockSharp LLC.
These signatures may be used in spam emails so you need to beware of them and avoid opening them as well as downloading the infected attachments.
You can use the removal guide given below as a reference to successfully eliminate VegaLocker ransomware from your computer.
Step_1: Restart your PC and boot into Safe Mode with Command Prompt by pressing F8 a couple of times until the Advanced Options menu appears.
Step_2: Navigate to Safe Mode with Command Prompt using the arrow keys on your keyboard. After selecting Safe Mode with Command Prompt, hit Enter.
Step_3: After loading the Command Prompt type cd restore and hit Enter.
Step_4: After cd restore, type in rstrui.exe and hit Enter.
Step_5: A new window will appear, and then click Next.
Step_6: Select any of the Restore Points on the list and click Next. This will restore your computer to its previous state before being infected with the VegaLocker Ransomware. A dialog box will appear and then click Yes.
Step_7: After System Restore has been completed, try to enable the disabled Windows services.
- Press Win + R keys to launch Run.
- Type in msc in the box and press Enter to open Group Policy.
- Under Group Policy, navigate to:
- User Configuration\Administrative Templates\System
- After that, open Prevent access to the command prompt.
- Select Disable to enable cmd
- Click the OK button
- After that, go to:
- Configuration\Administrative Templates\System
- Double click on the Prevent Access to registry editing tools.
- Choose Disabled and click OK.
- Navigate to :
- User Configuration\Administrative Templates\System>Ctrl+Alt+Del Options
- Double click on Remove Task Manager.
- And then set its value to Disabled.
Step_8: Open Task Manager by pressing Ctrl + Shift + Esc at the same time. Proceed to the Processes tab and look for the malicious processes of VegaLocker Ransomware and end them all.
Step_9: Open Control Panel by pressing Start key + R to launch Run and type appwiz.cpl in the search box and click OK to open the list of installed programs. From there, look for VegaLocker ransomware or any malicious program and then Uninstall it.
Step_10: Tap Windows + E keys to open the File Explorer then navigate to the following directories and delete the malicious files created by VegaLocker ransomware such as Your files are now encrypted.txt, temp.txt, masterblankov24.exe, [random].exe.
- %UserProfile%\AppData
- %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup
- %TEMP%.
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
Step_11: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech-savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you trouble and time, you can just use Restoro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step_12: Tap Win + R to open Run and then type in Regedit in the field and tap enter to pull up Windows Registry.
Step_13: Navigate to the paths listed below and delete all the registry values added by VegaLocker ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step_14: Close the Registry Editor and empty your Recycle Bin.
Congratulations, you have just removed VegaLocker Ransomware in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
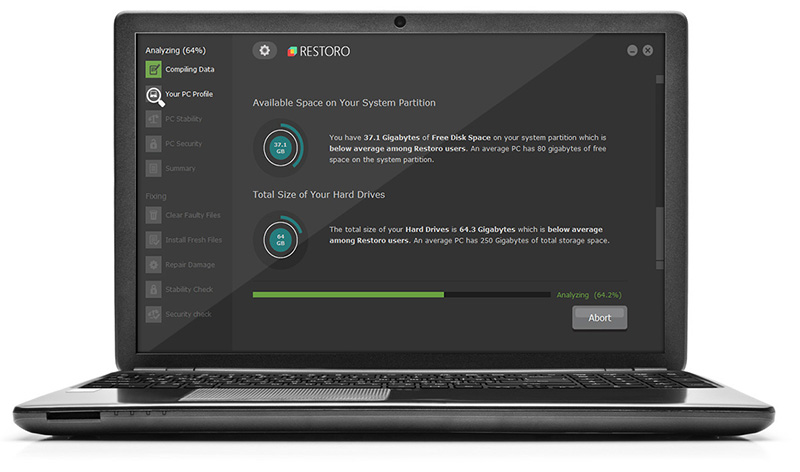
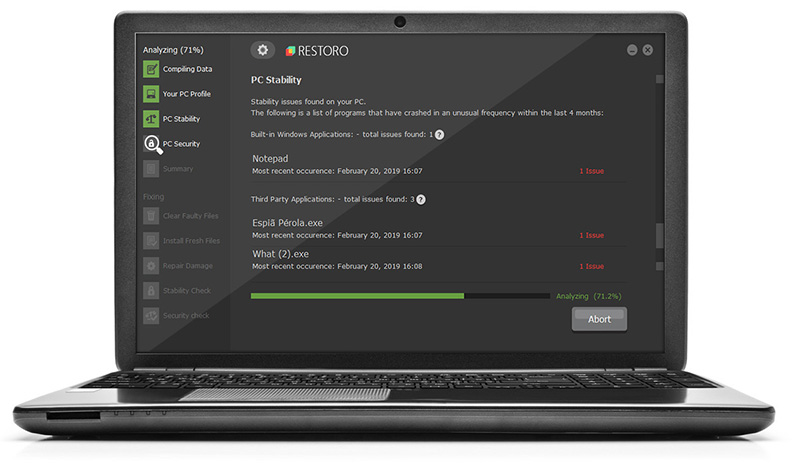
Now that’s how you remove VegaLocker Ransomware in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.