What is Google.exe Miner? And how does it function?
Google.exe Miner is a malicious program classified as a Trojan horse that is used to mine digital crypto-currencies on the compromised PC. To put it simply, Google.exe Miner Trojan is used by cybercrooks to earn digital money called Monero by using the infected computer’s resources without the user knowing. Technically, are not really classified as an unsafe program by default as there are tons of open source solutions that allow regular PC users to use an old network or PC to earn money – however, with the rise in Bitcoin prices, it is perceived to be the motivation for cybercriminals to develop malicious threats like this one.
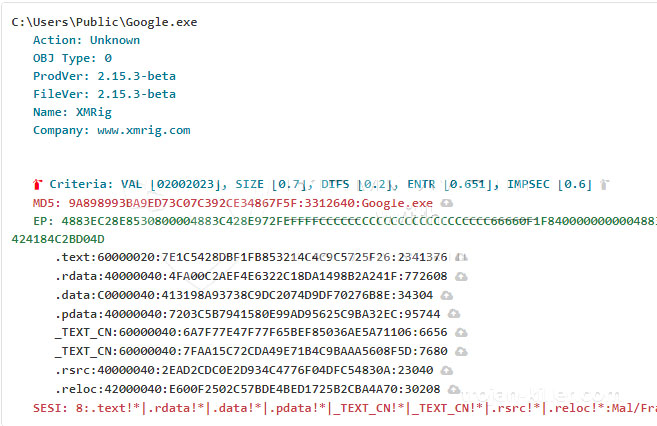
As soon as it invades the system, it launches the Google.exe process to start mining CPU resources for crypto-currency. Such activity will slow the affected computer down, constant lags, software crashes, and other intolerable system issues. So if you noticed your computer’s performance suddenly took a dive down, then you should check your PC for Google.exe Miner as soon as possible.
Malicious cryptocurrency mining tools like Google.exe Miner allow cybercriminals in generating more substantial amounts of money with the help of a botnet of a victim’s computer that is infected with this Trojan. What’s disturbing is that this program can run in your computer unnoticeably for months or even years, which earns the profit for the crooks behind it, all the while affecting your computer’s performance as it slowly starts to deteriorate.
If you are one of the users infected with Google.exe Miner, take note that there really is no outward indication that your computer is indeed infected. However, you will not miss the sudden slowness of your computer. Programs on your computer do not open as quickly as before. Thus, if you want to use your computer as efficiently like you used to and prolong your CPU’s life, then you need to terminate this Trojan horse from your computer right away.
How does Google.exe Miner circulate the web?
Google.exe Miner spreads through software bundles. It is added as an extra program in a software package. Meaning to say, you can get infected with this Trojan infection when you install software bundles using only the quick or standard setup instead of the recommended Advanced or Custom setup – this setup allows you to deselect any extra programs added in the bundle. So if you are still planning on installing software bundles or freeware and shareware in the future, make sure that you always opt for the recommended setup instead of rushing the installation with the quick setup.
Kill the Google.exe Miner from your computer using the removal guide prepared below.
Step_1: Tap Ctrl + Shift + Esc keys to open the Windows Task Manager.
Step_2: Go to the Processes tab and look for the malicious processes named “Google.exe”, as well as other suspicious-looking processes, and then right-click on each one of these malicious processes and select End Task.
Step_3: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in “appwiz.cpl” and then click OK or press Enter.
Step_4: Look for dubious programs that might be related to the Google.exe Miner and then Uninstall it/them.
Step_5: Close Control Panel and then tap Win + E to launch File Explorer.
Step_6: After opening File Explorer, navigate to the following directories below and look for Google.exe Miner’s malicious components such as the Google.exe and other suspicious-looking files and then erase them all.
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- C:\ProgramData\local\
Step_7: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech-savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you trouble and time, you can just use Restoro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step_8: Tap Win + R to open Run and then type in Regedit in the field and tap enter to pull up Windows Registry.
Step_9: Navigate to the listed paths below and look for the registry keys and sub-keys created by Google.exe Miner.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step_10: Delete the registry keys and sub-keys created by Google.exe Miner.
Step_11: Close the Registry Editor.
Step_12: Empty your Recycle Bin.
Congratulations, you have just removed Google.exe Miner Crypto-Miner in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
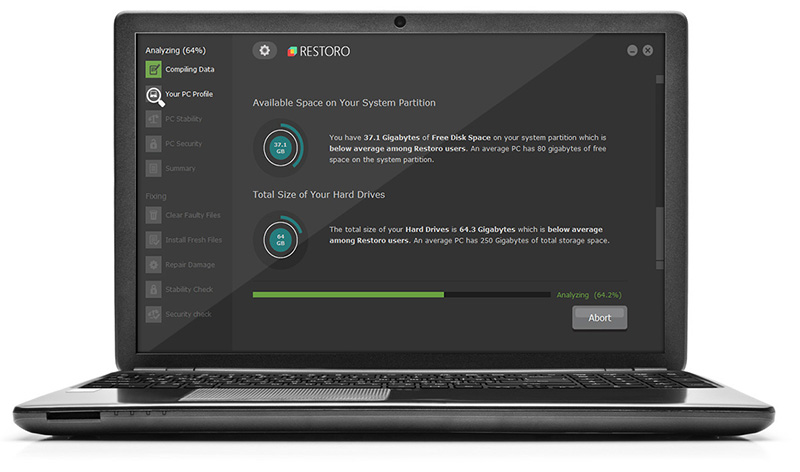
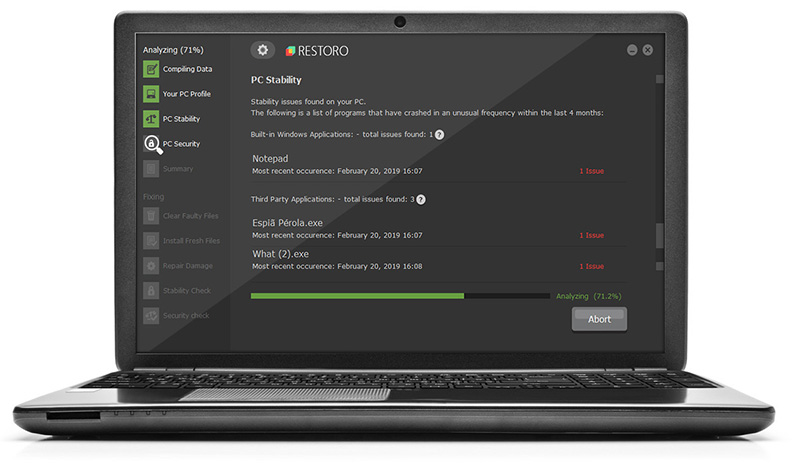
Now that’s how you remove Google.exe Miner Crypto-Miner in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.