What is MegaLocker ransomware? And how does it carry out its attack?
MegaLocker ransomware is a dangerous file-encrypting virus that was recently discovered. It is encrypted valuable files in a targeted machine using a sophisticated encryption algorithm, AES-CBC 128, and appends the “.crypted” extension.
It begins to execute its attack by connecting to a remote server controlled by the attackers. From there, it downloads malicious files and places them on system folders. These malicious files are then used to make sure that no program installed on the computer can interfere with the attack. Some of these files are also used to make alterations in the registry so that the crypto-malware can run automatically on every system startup.
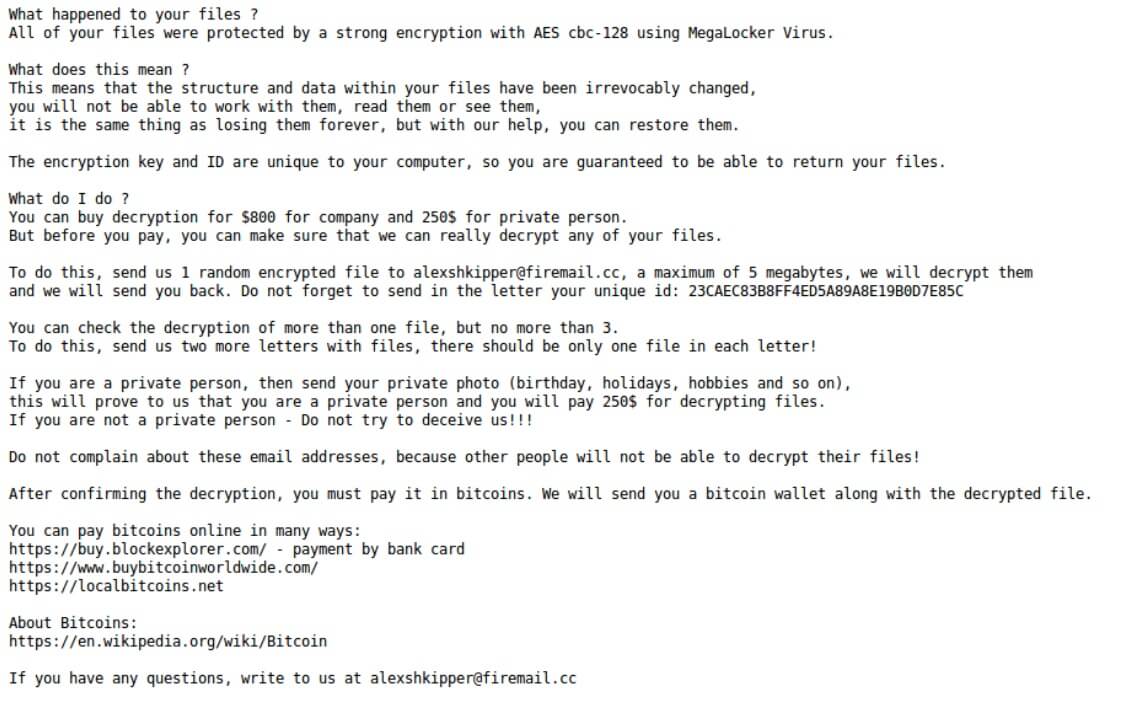
It then scans the computer in search of its targeted files. It may target documents, databases, images, videos, audio files, archives, and other user-generated files. After the encryption, it adds the .crypted suffix at the end of every encrypted file’s name. Following the encryption, it drops a text file named “! DECRYPT_INSTRUCTION.txt” which contain the ransom note that states:
“All your files were protected with strong encryption using AES CBC-128 using MegaLocker Virus.
What does it mean?
This means that the structure and data in your files have been irrevocably changed,
you cannot work with them, read them or see them,
this is the same as losing them forever, but with our help, you will be able to recover them.
The encryption key and ID are unique to your computer, so you are guaranteed to be able to get your files back.
What should I do?
You can buy a transcript for $ 800 for a company and $ 250 for a private individual.
But before paying, you can make sure that we really can decrypt any of your files.
To do this, send us 1 random encrypted file at [email protected], a maximum of 5 megabytes, we will decrypt them
and we will send you back. Do not forget to send in a letter your unique id: 23CAEC83B8FF4ED5A89A8E19B0D7E85C
You can check the decryption of more than one file, but no more than 3.
To do this, send us two more letters with files, each letter should contain only one file!
If you are a private person, send your personal photo (birthday, holidays, hobbies, etc.),
this will prove to us that you are a private person, and you will pay $ 250 for decrypting files.
If you are not a private person – do not try to deceive us !!!
Do not complain about these email addresses, because other people will not be able to decrypt their files!
After confirming the decryption, you must pay it in bitcoins. We will send you a bitcoin wallet along with the decrypted file.
You can pay for bitcoins online in different ways:
https://buy.blockexplorer.com/ – payment by credit card
https://www.buybitcoinworldwide.com/
https://localbitcoins.net
About bitcoins:
https: //en.wikipedia. org / wiki / Bitcoin
If you have any questions, email us at [email protected]”
How does MegaLocker ransomware spread online?
MegaLocker ransomware might spread online using malicious spam email campaigns. This isn’t a surprise as this method is commonly used by ransomware developers. Usually, crooks attach an obfuscated file that contains malicious scripts used to install MegaLocker ransomware in the system. This is why it is advised to always double-check emails before you open them. It would also be better if you keep both your operating system and antivirus programs up-to-date to avoid ransomware infection.
To wipe out MegaLocker ransomware from your compromised computer successfully, follow the removal guide laid out below as well as the advanced steps that come next.
Step_1: First, restart your PC and boot into Safe Mode with Command Prompt by tapping F8 a couple of times until the Advanced Options menu appears.
Step_2: Next, navigate to Safe Mode with Command Prompt using the arrow keys on your keyboard. After selecting Safe Mode with Command Prompt, hit Enter.
Step_3: After loading the Command Prompt type cd restore and hit Enter.
Step_4: After cd restore, type in rstrui.exe and hit Enter.
Step_5: A new window will appear, and then click Next.
Step_6: Select any of the Restore Points on the list and click Next. This will restore your computer to its previous state before being infected with the MegaLocker Ransomware. A dialog box will appear and then click Yes.
Step_7: After System Restore has been completed, try to enable the disabled Windows services.
- Press Win + R keys to launch Run.
- Type in gpedit.msc in the box and press Enter to open Group Policy.
- Under Group Policy, navigate to:
- User Configuration\Administrative Templates\System
- After that, open Prevent access to the command prompt.
- Select Disable to enable cmd
- Click the OK button
- After that, go to:
- Configuration\Administrative Templates\System
- Double click on the Prevent Access to registry editing tools.
- Choose Disabled and click OK.
- Navigate to :
- User Configuration\Administrative Templates\System>Ctrl+Alt+Del Options
- Double click on Remove Task Manager.
- And then set its value to Disabled.
Step_8: Next, tap Ctrl + Shift + Esc to open the Task Manager and then go to the Processes tab and look for the malicious processes of MegaLocker Ransomware and end them all.
Step_9: Open Control Panel by pressing Start key + R to launch Run and type appwiz.cpl in the search box and click OK to open the list of installed programs. From there, look for MegaLocker ransomware or any malicious program and then Uninstall it.
Step_10: Tap Windows + E keys to open the File Explorer then navigate to the following directories and delete the malicious files created by MegaLocker ransomware such as “! DECRYPT_INSTRUCTION.txt” and “[random].exe”.
- %UserProfile%\AppData
- %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup
- %TEMP%.
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
Step_11: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech-savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you trouble and time, you can just use Restoro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step_12: Tap Win + R to open Run and then type in Regedit in the field and tap enter to pull up Windows Registry.
Step_13: Navigate to the paths listed below and delete all the registry values added by MegaLocker ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step_14: Close the Registry Editor and empty your Recycle Bin.
Congratulations, you have just removed MegaLocker Ransomware in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
Now that’s how you remove MegaLocker Ransomware in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
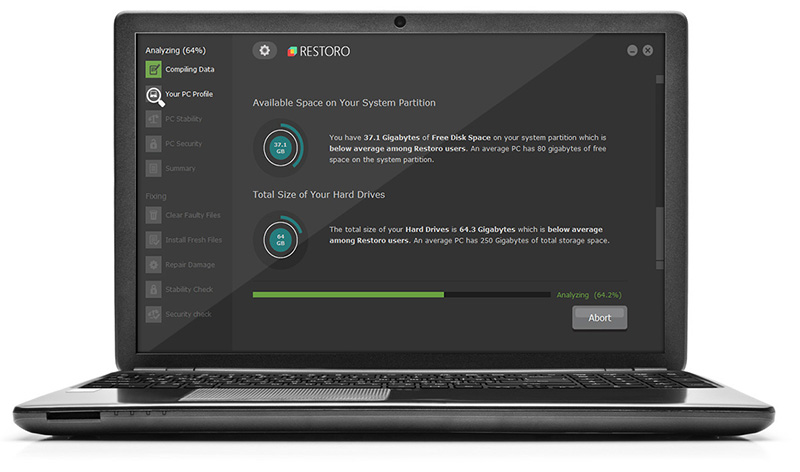
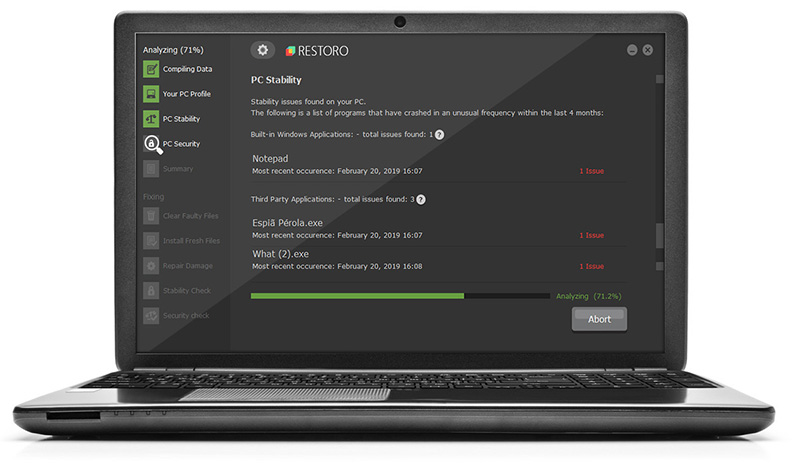
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.