What is OnyxLocker ransomware? And how does it carry out its attack?
OnyxLocker ransomware is a data-encrypting virus that attaches a “.onx” suffix to every file it encrypts. It isn’t known yet if it belongs to any ransomware groups, although based on the analysis done by security experts, it uses a sophisticated encryption algorithm in locking its targeted files. It seems to be targeting Russian-speaking users since its ransom note is written in the Russian language.
The instant it invades a computer, OnyxLocker ransomware will begin to carry out its nefarious attack by dropping its malicious payload in one of the system folders and launches it. It will also connect the infected computer to a remote server controlled by the attackers. From this remote server, the crypto-malware downloads more of its malicious components. After that, it uses an information-gathering module in order to gather data about the infected system and its user. The obtained data, along with some of the malicious components are then used for stealth protection. In addition, it also modifies some Registry entries so that it can run on every system boot.
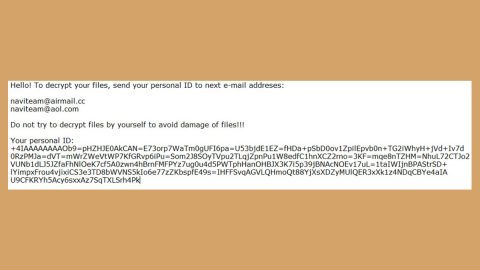
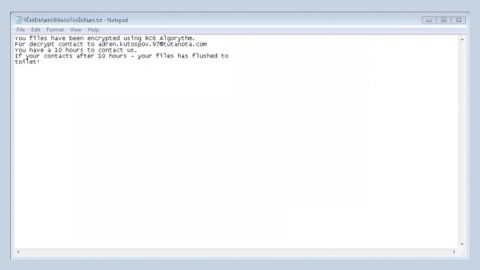
Once all these modifications are applied, it starts the encryption process by scanning the computer for files with certain extensions. After it finds the files it’s looking for, it encrypts them using the AES encryption algorithm. It then marks the encrypted files with the .onx extension. Following encryption, it drops 10 identical ransom notes like “Прочти меня! 0 .txt”, “Прочти меня! 1 .txt”, and so on, which contains the following content written in Russian:
“Моя почта для связи: [email protected]
|||
Меня зовут David. Я зашифровал все ваши драгоценные файлы, включая изображения, видео, песни, текстовые файлы, текстовые файлы и многое другое! Короче говоря, вы облажались … но вам повезло. Почему это??
|||
Я вымогатель, который оставляет вам только 12 часов, чтобы собрать деньги и заплатить мне, затем ваши файлы будет невозможно расшифровать!)
|||
Любые вопросы относительно разблокировки файлов, вы можете задавать написав на почту: [email protected]
|||
ЧАСТО ЗАДАВАЕМЫЕ ВОПРОСЫ:
|||
1. Могу ли я вернуть свои драгоценные файлы?
|||
Ответ: Конечно, вы можете. Есть только незначительная деталь. Вы должны заплатить, чтобы вернуть их.
|||
2. Нет другого способа вернуть мои файлы?
|||
Ответ: Нет
|||
3. Хорошо, что мне тогда делать?
Ответ: Просто вам придется заплатить 100 $ на этот биткойн-адрес: 3LV85h9s2y5c5DLi3YiACDKaR3tytmp3Lq
|||
4. Что за хрень биткойн?
|||
Ответ: Биткойн – это криптовалюта и цифровая платежная система. Вы можете увидеть больше информации здесь: hxxps://en.wikipedia.org/wiki/Bitcoin.
|||
5. Здесь вы можете оплатить, выбрав самый выгодный курс.
|||
Вставьте эту ссылку в адресную строку вашего браузера: hxxps://www.bestchange.ru/visa-mastercard-rur-to-bitcoin.html”
You must not, under any circumstance, pay the ransom demanded by the crooks behind OnyxLocker ransomware since it doesn’t really guarantee that you’ll recover your files. The best way to deal with this kind of cyber threat is by eliminating it from the computer the moment you’ve discovered it infected your computer after that, you can try alternative ways to restore the affected file without having to spend a cent.
How does OnyxLocker ransomware spread over the web?
OnyxLocker ransomware is believed to be distributed via malicious spam email campaigns. This means that it uses a corrupted attachment to infect computers. Cybercriminals typically disguise the malware-laden attachment as a receipt, invoice, bank statement, and so on to lure you into downloading and opening it. Once you open the file, it will execute malicious scripts used to launch OnyxLocker ransomware on the computer.
You can wipe out OnyxLocker ransomware from your computer by following the removal steps provided below and the advanced steps that follow.
Step_1: First, you have to stop the malicious process of OnyxLocker ransomware by opening the Task Manager. To do that, simply tap Ctrl + Shift + Esc keys on your keyboard.
Step_2: Under the Task Manager, switch to the Processes tab and find the suspicious-looking process that takes up most of your CPU’s resources and is most likely related to OnyxLocker ransomware.
Step_3: After that, close the Task Manager.
Step_4: Tap Win + R, type in appwiz.cpl and click OK or tap Enter to open Programs and Features under Control Panel.
Step_5: Under the list of installed programs, look for OnyxLocker ransomware or anything similar, and then uninstall it.
Step_6: Next, close the Control Panel and tap Win + E keys to launch File Explorer.
Step_7: Navigate to the following locations below and look for OnyxLocker ransomware’s malicious components such as “Прочти меня! 0 .txt”, “Прочти меня! 1 .txt” and “[random].exe”, as well as other suspicious files, then delete all of them.
- %TEMP%
- %WINDIR%\System32\Tasks
- %APPDATA%\Microsoft\Windows\Templates\
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
Step_8: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech-savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you trouble and time, you can just use Restoro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then, by all means, go on to the next steps.
Step_9: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.
Step_10: Navigate to the following path:
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step_11: Delete the registry keys and sub-keys created by OnyxLocker ransomware.
Step_12: Close the Registry Editor and empty the Recycle Bin.
Try to recover your encrypted files using the Shadow Volume copies
Restoring your encrypted files using Windows Previous Versions feature will only be effective if OnyxLocker ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.
Congratulations, you have just removed OnyxLocker Ransomware in Windows 10 all by yourself. If you would like to read more helpful articles and tips about various software and hardware visit fixmypcfree.com daily.
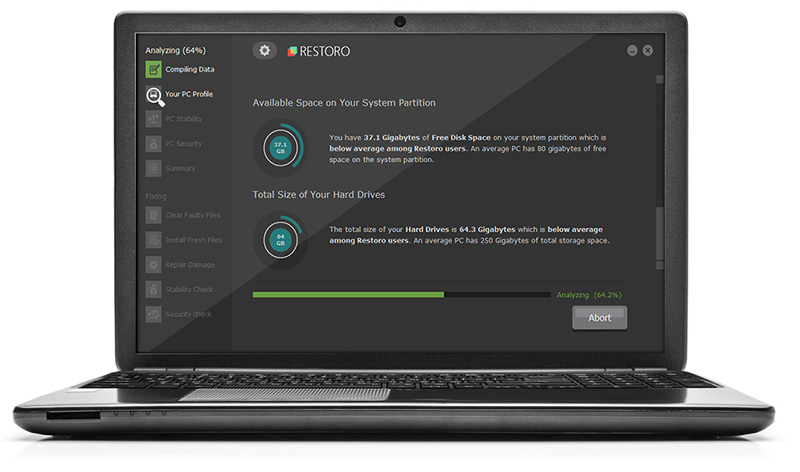
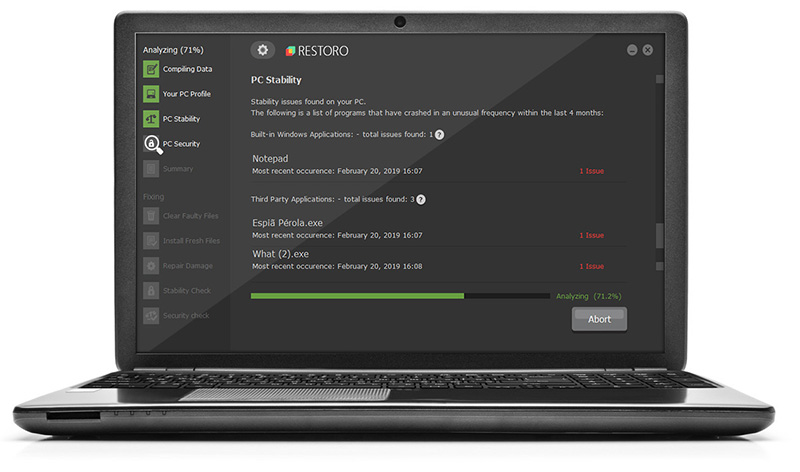
Now that’s how you remove OnyxLocker Ransomware in Windows 10 on a computer. On the other hand, if your computer is going through some system-related issues that have to get fixed, there is a one-click solution known as Restoro you could check out to resolve them.
This program is a useful tool that could repair corrupted registries and optimize your PC’s overall performance. Aside from that, it also cleans out your computer for any junk or corrupted files that help you eliminate any unwanted files from your system. This is basically a solution that’s within your grasp with just a click. It’s easy to use as it is user-friendly. For a complete set of instructions in downloading and using it, refer to the steps below
Perform a full system scan using Restoro. To do so, follow the instructions below.