What is Noblis ransomware? And how does it implement its attack?
Noblis ransomware is a ransomware Trojan set to encrypt files in a compromised PC. it mainly targets Spanish users as its ransom note is written in Spanish. According to the latest reports, this ransomware is still in its development phase so it isn’t being actively distributed yet. But it will be spreading soon enough once its developers have completed its finishing touches to the ransomware. It is most likely to spread in an obfuscated file named noblis.exe which might soon spread using malicious spam email campaigns.
Once it infiltrates the system, Noblis ransomware will make some changes in the system to achieve persistence. It will most probably target files with these formats:
.3dm, .3g2, .3gp, .7zip, .aaf, .accdb, .aep, .aepx, .aet, .ai, .aif, .as, .as3, .asf, .asp, .asx, .avi, .bmp, .c, .class, .cpp, .cs, .csv, .dat, .db, .dbf, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dwg, .dxf, .efx, .eps, .fla, .flv, .gif, .h, .idml, .iff, .indb, .indd, .indl, .indt, .inx, .jar, .java, .jpeg, .jpg, .js, .m3u, .m3u8, .m4u, .max, .mdb, .mid, .mkv, .mov, .mp3, .mp4, .mpa, .mpeg, .mpg, .msg, .pdb, .pdf, .php, .plb, .pmd, .png, .pot, .potm, .potx, .ppam, .ppj, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prel, .prproj, .ps, .psd, .py, .ra, .rar, .raw, .rb, .rtf, .sdf, .sdf, .ses, .sldm, .sldx, .sql, .svg, .swf, .tif, .txt, .vcf, .vob, .wav, .wma, .wmv, .wpd, .wps, .xla, .xlam, .xll, .xlm, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xqx, .xqx, .zip.
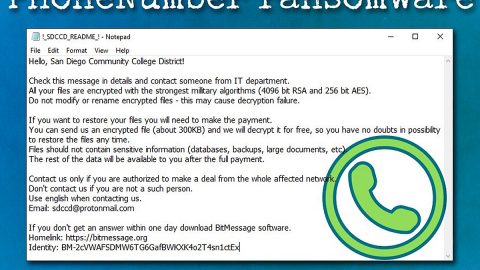
Once the file-encrypting malware finishes its search for the file formats to target, it begins its encryption attack using a strong encryption algorithm which is currently unknown. After its disruptive attack, it opens a program window which has a timer and is written in Spanish:
“CRYPTER
YOUR FILES HAVE BEEN ENCRYPTED!
Los archivos más importantes de este equipo han sido cifrados con un sistema de grado militar (AES-256)
Sus documentos, videos, imágenes y otros formatos (y por supuesto la FLAG) están fuera de su alcance… Y no podrá descifrarlos sin la llave apropiada… Esta se encuentra almacenada en un servidor remoto.
Las únicas formas de obtenerla, será pagando a la billetera antes que el tiempo se acabe.. También puede vulnerar el servidor remoto¿?…
O encontrar alguna falla en este sistema de cifrado¿?…
— Recuerde que este reto es únicamente con fines académicos e investigativos… No pierda tiempo… Pues una vez termine la cuenta regresiva, los archivos serán eliminados de forma permanente —
@4v4t4r
WALLET ADDRESS: nobliswallet99838399283928392323
BITCOIN FEE: 1.0”
Based on its ransom note, its final sentences states that Noblis ransomware was created for academic and research purposes which isn’t true as it obviously encrypts the files in its targeted computer. It even demands a ransom to a Bitcoin address which apparently is a wrong address so there is no point in contacting these crooks. You must immediately remove Noblis ransomware from your computer as soon as you notice it.
How does Noblis ransomware proliferate?
As pointed out earlier, Noblis ransomware will probably spread using the most common distribution method used by cybercriminals in spreading ransomware infections which is through spam emails. Beware that the email may contain a malicious executable file named noblis.exe.
Eliminate Noblis ransomware by following these removal steps:
Step 1: Close the program window of Noblis ransomware and tap the Win + E keys to open File Explorer.
Step 2: Navigate to the following locations and look for the file named noblis.exe, which is the malicious executable file used to install Noblis ransomware into the computer.
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- %HOMEDRIVE%\user | ransom.jpg
- %USERPROFILE%\Desktop | READ_IT.txt
Step 3: Close the File Explorer and tap Ctrl + Shift + Esc keys to open the Task Manager.

Step 4: After opening the Task Manager, look for Noblis ransomware’s malicious process, right click on it and select End Process or End Task.

Step 5: Close the Task Manager.
Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use PC Cleaner Pro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then, by all means, go on to the next steps.
Step 6: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 7: Navigate to the following path:
HKU\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
Step 8: Look for any suspicious values created by Noblis ransomware and delete them.
Step 9: Close the Registry Editor and open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.
Step 10: Look for Noblis ransomware or any suspicious program and then Uninstall it/them.

Step 11: Empty your Recycle Bin.
Try to recover your encrypted files using the Shadow Volume copies
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if Noblis ransomware hasn’t deleted the shadow volume copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
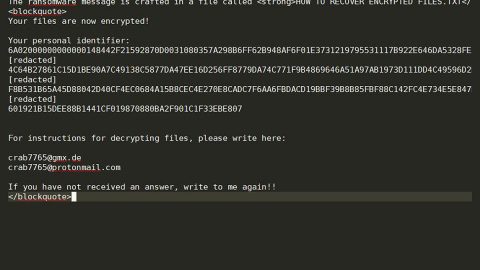
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

Ensure the removal of Noblis ransomware from your computer as well as the malicious files it created with the help of the advanced removal instructions below.
Perform a full system scan using SpyRemover Pro. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading the program. Installation will start automatically once download is done.
- Click OK to launch it.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register the program to protect your computer from future threats.