If you’re reading this blog, then I already know you’re a smart PC user.
Most PC users don’t bother looking up PC tips online, or learning how to speed up and optimize their computers. But you do.
Unfortunately, even smart PC users like you are falling for this latest phishing attack. This sophisticated attack uses Dropbox and a legitimate-looking domain to trick internet users into divulging personal information.
And it’s working.
Even tech-savvy PC users are falling for this scam. Below, you’ll see why it’s so clever.
How it works
This latest phishing attack relies on a complicated series of events carefully designed to trick the user into letting down his or her defenses:
-The attack begins with a new email in your inbox. The subject of that email simply says “important”
-When you open the email, you get a message saying the recipient has been sent a document that is too big to be sent by email, or that it cannot be sent by email for security reasons (the specific message varies in order to get past spam filters).
-Next, the email claims that users can click the link included in the message to open the document.
-When you click that link, you visit a fake Dropbox login page. But here’s the real tricky part: that login page is hosted on Dropbox itself.
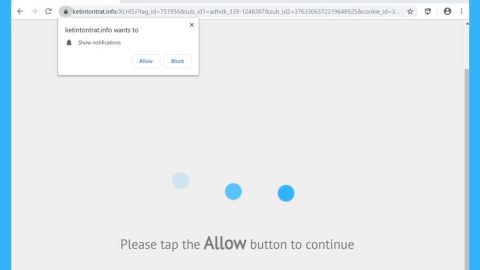
-In other words, you see a fake login page, but if you look at the address bar, you see Dropbox.com. Here’s what this looks like in practice:

-Tough to spot, right? The fake login page is hosted on Dropbox’s user content domain, which is typically used to share photos and other files. Making things even trickier is the fact that the page is served over SSL, so you see a convincing “https” in the address bar.
-I haven’t even got to the worst part of this scam: the hackers have included the logos of popular email applications like Yahoo and Gmail directly over top of the credential login form, making it seem like you can login using your email address and email password.
-If you do happen to enter that information, the form sends your data to a PHP script before submitting your information via SSL. That SSL encryption process is important, because it prevents users from seeing the following warning message:

-This hack is neat and tidy too. Once the PHP script has gone through, users are simply redirected to the main, legitimate Dropbox login page, making it seem like there was just a momentary problem and you can solve it by logging in once again. So your information might be stolen without any warning signs going off in your head.
How to avoid this scam
Ultimately, even the smartest PC users can be fooled by this scam. After all, two things smart people are taught to look for in phishing attacks are “https” in the address bar and the real website in the address bar.
So how do you avoid this attack? The best way is to avoid opening any links from unknown senders. The other option is to make sure you’re at Dropbox.com (or other official websites) with nothing suspicious before or after in the address bar.
Fortunately for you, Dropbox has removed the offending pages. More can pop up at any moment, however, so keep an eye out for any Dropbox-hosted phishing pages and report them to [email protected] if found.
Shout out to Symantec for spotting this issue and writing up a detailed explanation of how to solve it.