What is JabaCrypter ransomware? And how does it implement its attack?
JabaCrypter ransomware is a dangerous crypto-malware that employs the AES cipher to lock targeted files and demands ransom for their file recovery. This new ransomware threat is among the other ransomware infections discovered in the last week of April 2018. According to security experts, it mainly targets Russian-speaking users as its ransom note is written in Russian.
As soon as JabaCrypter ransomware infiltrates a system, it will start to implement its attack by scanning the entire drive of the computer with the goal of finding user-generated files and encrypting them using the AES encryption algorithm. After it encrypts targeted files, it appends the .cryptfile extension to each one of them and drops a ransom note named “ReadMe.html” that is written in Russian – it states:
“Отчёт: Все ваши файлы успешно зашифрованны.
Без паники, Дамы и Господа!
———————————–
Все ваши файлы и базы успешно зашифрованны нашим хитрожопым криптером.
Расшифровка всего вашего добра не имея уникального “расшифровщика” практически НЕВОЗМОЖНА!, Вы просто уничтожите все ваши данные.
Если вы не жадный, а очень щедрый человек, то мы готовы обменять всю вашу драгоценную информацию на жалкие бумажки именуемые бабками.
Поверьте бабло, побеждает зло, отдайте его нам.
———————————–
По вопросу приобретения “расшифровщика” писать на почту:
[email protected]
В письме – не забудьте указать ваш “id” указанный в конце каждого зашифрованного файла.
Мы бесплатно расшифруем несколько ваших файлов, что бы вы убедились что дешифратор у нас есть, возможно будет и у вас.
———————————–
© 2018 Всё будет хорошо!”
Ransom note translated into English:
“Report: All your files are successfully encrypted.
Without panic, Ladies, and Gentlemen!
———————————–
All your files and databases are successfully encrypted by our sly-ass cryptor.
Deciphering all your goods without having a unique “decryptor” is virtually impossible ! you simply destroy all your data.
If you are not greedy, but a very generous person, then we are ready to exchange all your precious information for a pathetic paper called bucks.
Believe me, the loot wins the evil, give it to us.
———————————–
On the acquisition of “decryptor” write to the mail: [email protected]
In the letter – do not forget to indicate your “id” specified at the end of each encrypted file.
We will decrypt for free several of your files so that you can make sure that we have the decoder, maybe he will be by you.
———————————–
© 2018 Everything will be fine!”
The crooks behind JabaCrypter ransomware are urging victims to contact them at the email address given in the ransom note so that they’ll be given the exact ransom amount. Even so, you are definitely not advised to give into the demands of these crooks as they can’t be trusted. It’s best if you eliminate JabaCrypter ransomware from your system first and then try other ways to recover your encrypted files without spending money.
How is the malicious payload of JabaCrypter ransomware distributed?
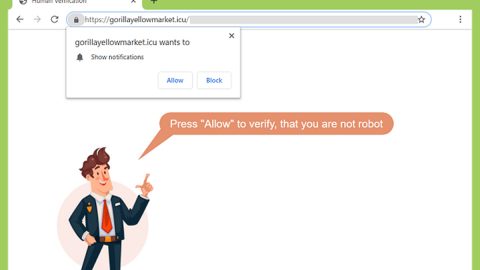
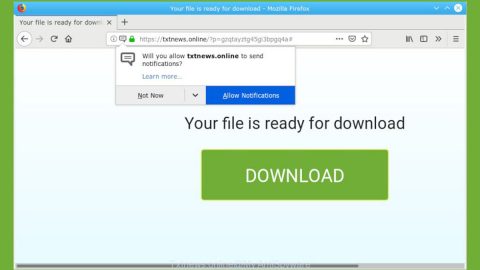
This dangerous ransomware can reach your system via spam emails. So if you carelessly open emails and download their attachment without checking anything, then it’s no wonder your computer is infected with JabaCrypter. Cybercrooks tend to disguise their malware-laden emails to lure users into opening them and downloading the corrupted attachment. So the next time you see any funny-looking or suspicious-looking emails, make sure to delete them right away.
For the successful removal of JabaCrypter ransomware, follow the given steps below.
Step 1: Tap Ctrl + Shift + Esc keys to launch the Task Manager.
Step 2: Go to Processes and look for the malicious process of JabaCrypter ransomware then right click on it and select End Process or End Task.

Step 3: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.
Step 4: Look for dubious programs that might be related to JabaCrypter ransomware and then Uninstall it/them.

Step 5: Tap Win + E to launch File Explorer.
Step 6: From there, navigate to the following directories listed below and look for the malicious components of JabaCrypter ransomware like its ransom note in an HTML file that means “ReadMe.html” and remove them all.
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- C:\ProgramData\local\
Step 7: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use [product-name], this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then, by all means, go on to the next steps.
Step 8: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 9: Navigate to the listed paths below and look for the registry keys and sub-keys created by JabaCrypter ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step 10: Delete the registry keys and sub-keys created by JabaCrypter ransomware.
Step 11: Close the Registry Editor.
Step 12: Empty your Recycle Bin.
Try to recover your encrypted files using the Shadow Volume copies
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if JabaCrypter ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

Complete the removal process of JabaCrypter ransomware by using a trusted and reliable program like [product-name]. Refer to the following guidelines on how to use it.
Perform a full system scan using [product-code]. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in the URL address, [product-url] in the Run dialog box and then tap Enter or click OK.
- After that, it will download the program. Wait for the download to finish and then open the launcher to install the program.
- Once the installation process is completed, run [product-code] to perform a full system scan.