What is Oni Ransomware? And how does it carry out its attack?
Oni ransomware is an extremely dangerous file-encrypting threat which mainly attacks medium-large Japanese companies. It has some similarities with the notorious Globe Imposter ransomware. It all started when Cybereason, a security firm, analyzed a couple of ransomware infected with a virus called Oni. This ransomware has already been analyzed long before Cybereason did but it wasn’t determined how its victims were being infected. After Cybereason’s analysis, they found that the infected computers were previously targeted by a spear phishing campaign which installs Remote Access Trojans or RATs on the infected computers. These phishing emails were disguised as receipts which has a ZIP file that contains a corrupted macro-enabled document. So when a user opens this document, a VBScript will appear that downloads and installs a copy of the Ammy Admin Remote Access Trojan into the compromised PC.
To be clear, Ammy Admin is a legitimate remote admin tool but in this case it is being used in a malicious way by the cyber crooks behind Oni ransomware. They use Ammy Admin to obtain access to the infected system. And based on Cybereason’s report, instances of this RAT were already being used as far back as December 2016 and recently on September 2017. Once access to the PC is obtained, they continue obtaining access to the domain administrator account and servers. And as of now it isn’t yet clear what the crooks were doing during the period of time they have access to the compromised network.
Once their hacking tasks are completed, that’s when they begin another attack. Since they already have access to domain servers, they will use the Group Policy Scripts to run a batch file to clean up their tracks that would clear up over 460 different event logs. They also use the very same script to deploy Oni ransomware on computers so they can start encrypting data and continue to obfuscate their activities.
What has security experts interested in this ransomware is that it’s unlike any other ransomware infection they’ve seen as it uses two different versions of Oni ransomware. The first one is mostly used to target non-critical computers which make it the same as Globe Imposter virus. After its encryption attack, Oni ransomware drops its ransom note in a file named !!!README!!!.html which is placed in folders where files were encrypted. The file contains the following message written in Japanese:
“重要な情報!
すべてのファイルは、RSA-2048およびAES-256暗号で暗号化されています。
心配しないで、すべてのファイルを元に戻すことができます。
すべてのファイルを素早く安全に復元できることを保証します。
ファイルを回復する手順については、お問い合わせ。
信頼性を証明するために、2ファイルを無料で解読できます。ファイルと個人IDを私たちにお送りください。
(ファイルサイズ10MB未満、機密情報なし)
連絡先
[email protected]”
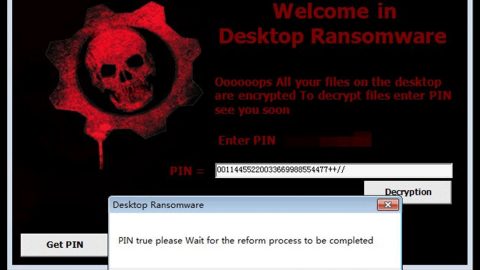
The second version is referred to as MBR-Oni as it meddles with the affected computer’s Master Boot Record – a technique used by NotPetya and Bad Rabbit ransomware infections. Based on Cybereason’s report, MBR-Oni is only deployed on active directory servers or what they call as “critical assets”. It encrypts the actual file system and replaces the MBR with a password protected lock screen before Windows boots containing the following text:
“Your data is ENCRYPTED!
You will not decrypt it without our help!
Your ID:
Contact us”
Passoword:”
Take note that removing Oni ransomware would be a really complicated task, nonetheless, you can still try eliminating it using the removal instructions below.
Step 1: Reboot your computer into Safe Mode with Command Prompt by pressing F8 a couple of times until the Advanced Options menu appears.

Navigate to Safe Mode with Command Prompt using the arrow keys on your keyboard. After selecting Safe Mode with Command Prompt, hit Enter.
Step 2: After loading the Command Prompt type cd restore and hit Enter.

Step 3: After cd restore, type in rstrui.exe and hit Enter.

Step 4: A new window will appear, and then click Next.

Step 5: Select any of the Restore Points on the list and click Next. This will restore your computer to its previous state before being infected with the Oni Ransomware.
Step 6: A dialog box will appear, and then click Next.

Step 3: After System Restore is completed, log into your computer and tap Ctrl + Shift + Esc keys to launch the Task Manager.
Step 4: Go to Processes and look for Oni ransomware’s malicious process, right click on it and select End Process or End Task.

Step 4: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.
Step 5: Look for dubious programs that might by related to Oni ransomware and then Uninstall it/them.

Step 6: Tap Win + E to launch File Explorer.
Step 7: After opening File Explorer, navigate to the following locations below and look for Oni ransomware’s malicious components such as !!!README!!!.html and the macro-enabled document you’ve downloaded from the spam email.
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
- %TEMP%
Step 8: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use PC Cleaner Pro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step 9: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 10: Navigate to the listed paths below and look for the registry keys and sub-keys created by Oni ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step 11: Delete the registry keys and sub-keys created by Oni ransomware.
Step 12: Close the Registry Editor and empty the Recycle Bin.
Follow the continued advanced steps below to ensure the removal of Oni Ransomware:
Perform a full system scan using SpyRemover Pro. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading the program. Installation will start automatically once download is done.
- Click OK to launch it.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register the program to protect your computer from future threats.