What is Scarab Ransomware?
The Scarab Ransomware is a typical encryption ransomware Trojan that was discovered on June 13, 2017 which is definitely new. The Scarab Ransomware is one of the currently active HiddenTear variants. HiddenTear, is an open source ransomware Trojan first released in year 2015 which has spawned countless threat variants since its code was made easily available to amateur con artists looking to carry out these tricks for their attacks. Most commonly used way of distributing the Scarab Ransomware is through including it as a corrupted file attachment in spam email messages. Good thing, the Scarab Ransomware can be easily identified because it will appends the files it encrypts with the file extension ‘.scarab,’ which is included to the end of the affected file’s name. The the Scarab Ransomware is a little bit different from the other ransomware Trojans, which encrypt the victim’s files and then later demand payment of a certain amount in exchange for the decryption code that’s necessary to recover the affected files.
How Does Scarab Virus Infiltrate the Computer System?
The developers designed the Scarab virus with a single binary executable file so it’s easier to distribute and that can be spread using different methods depending on the targets and the required scale.
Commonly, one of the primary infection tactics employed by most ransomware like this one is through the spam email messages. Developers usually use social engineering strategies that make the users infect themselves unknowingly. They made the emails to appear as legitimate companies or could be as government institutions and usually carry the virus either attached or linked in the contents.
Another thing is the office documents and modified software installers can also carry the Scarab virus code. Basically, they are spread on hacked or hacker-controlled download sites and popular P2P networks such as the BitTorrent. Also, the hackers can also simply create web redirects and ad networks that redirect to them.
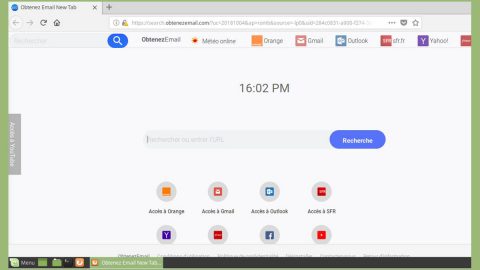
Browser hijackers and other malicious add-ons also may appear and can deliver the Scarab virus as part of their infection behavior.
Terminating Scarab Ransomware permanently
Generally, dealing with the infection’s developers is extremely dangerous and absolutely risky, and we advise you not to give them any single opportunity to trick you. Take note that there is no point to keep the malicious application on the system since this Scarab Ransomware was specifically designed to erase some of its created files from the infected computer, but for safety precautions, it would be wise to check if it actually deleted itself from the system. If it does not, then you can follow the removal guide provided below to locate the malware’s data, but also helps on how to get rid of it manually. On the other hand, you can opt to acquire a reputable anti-malware tool so you can eliminate this malicious application automatically; just do a full system scan and click the removal button.
It is basically imposed reaction to immediately eliminate the malware with the assistance of a security application and make sure it is updated.
How to Manually Erase Scarab Ransomware
- Press Windows Key+E.
- Navigate to these provided paths:
%APPDATA%
%TEMP%
%USERPROFILE%\desktop
%USERPROFILE%\downloads - Search for suspicious data that could be associated with the malware.
- Right-click such files and press Delete.
- Go to %USERPROFILE% and right-click a text document called IF YOU WANT TO GET ALL YOUR FILES BACK, PLEASE READ THIS.TXT and select Delete.
- Locate and remove all other ransom notes.
- Exit the File Explorer.
- Empty the Recycle bin.
- Reboot the system.
In simple terms:
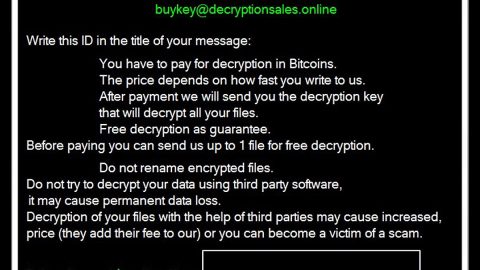
The Scarab Ransomware locks user’s data with a strong and complicated encryption algorithm, and it generates a decryption with which it is possible to decipher the locked files. Unluckily, the key should be saved on a secret server belonging to the malicious application’s creators where they kept securely so users cannot obtain it. And the hackers behind the malware do this so they could try to extort money from the victim user. Nonetheless, no matter how much you would wish to regain your data we advise and encourage you not to give in to their demands and keep your savings to yourself since there is always a possibility that these people could trick you and take the money without delivering the decryption key after. Instead of paying the ransom, you could try using special recovery tools or search for available copies on their removable media devices and some sort of storage. Just before any recovery attempts, it would be safest to eliminate the threat first with a reputable anti-malware tool or the removal guide located.
How to automatically remove Scarab Ransomware
These instructions indicate how to get rid of Scarab Ransomware automatically. The instructions need to be applied on the infected computer.
- Turn the infected computer on. If it is turned on, restart it.
- When BIOS screen disappears after the reboot, tap F8 key repeatedly. Advanced Options menu will show up. If Windows logo appears, reboot the PC and try pressing F8 again.
- When you access Advanced Options menu, use arrow keys to navigate and choose Safe Mode with Networking. Press Enter to access the mode.

4. Wait for Windows to load Safe Mode with Networking.
5. Press and hold the Windows key and then press R key.


6. If you have pressed both keys correctly, Windows Run Box will pop up.
7. Type the following into the Open box:
explorer https://www.fixmypcfree.com/removal
*Note, that there has to be a single space gap in between iexplore and http. Click OK.
8. Internet Explorer will open and a download dialog bar will appear at the bottom of your screen. Click Run to begin the installation automatically once SpyRemover Pro is downloaded.

9. Click OK if your system asks whether you want to run SpyHunter software.
10. Run SpyHunter and perform a full system scan.
11. Once all the malicious infections are detected, click Fix Threats. SpyHunter will ask you to register the software.
12. By registering SpyHunter you will also be able to protect your computer from other potential threats. Once you have registered the program, the malware will be removed. Reboot your PC to fully implement the malware removal procedure.