What is Torpig? And how does it function?
Torpig is a notorious Trojan infection which was first discovered in 2005. Since then, security experts managed to shut this Trojan horse down for a decade. However, its developers are back with its new and improved version which is even more menacing than before. The new version of Torpig is known as Anserin or Sinowal and is responsible for the extortion of personal data like credit card credentials, passwords, login details, and other similar information that would allow Torpig’s developers to take full control of a targeted system later on.
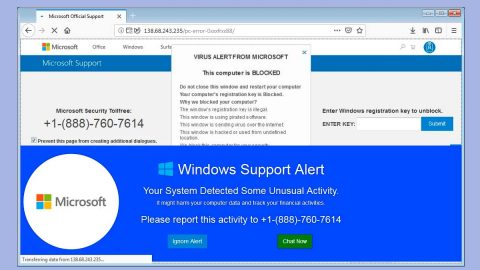
This Trojan infection can render an antivirus program useless – that’s how dangerous it is. It can also delete some important system files and disable some processes as well as extensions of some personal files like documents, videos or audio files. One of the first things you’ll notice when you try to remove this Trojan is that your system will be unable to launch a scan using your antivirus program or you might not be able to open it at all. Aside from that, Torpig can also block any security-related websites on a web browser and prevent download of antivirus programs, anti-malware and optimization tools with a built-in antivirus function.
Security experts have agreed that Torpig is will definitely make it on history books as it is one of the most notable credit card and bank account theft with over a total of 500,000 attacks on online banks and credit cards as well as debit ones ten years ago.
How does Torpig spread online?
Torpig spread via spam emails. Emails created by developers of this Trojan contain a .docx attachment with macro scripts. As soon as you open this macro-enabled document, Torpig ransomware will be downloaded and installed in the system. Note that this malware can only be activated if you agree in enabling Macros. So as much as possible, it would be best if you avoid opening any kinds of emails especially if the email contains a dubious .docx file.
Moreover, to keep your system safe and avoid threats similar to Torpig, it would be better if you always keep both your system and antivirus program up-to-date.
Carefully follow the removal guide laid out below so you can remove the Torpig Trojan from your system successfully.
Step 1: Tap Ctrl + Shift + Esc keys on your keyboard to pull up the Task Manager

Step 2: After opening the Task Manager is opened, go to the Processes tab and locate the malicious process of Torpig and end all of them.

Step 3: Close the Task Manager and tap the Win + R, then type in appwiz.cpl and then tap Enter or click OK to open Control Panel.
Step 4: Look for Torpig and then uninstall it.

Step 5: Close Control Panel and then tap the Win + E keys to open File Explorer.
Step 6: Navigate to the following locations.
- %HOMEDRIVE%\Applications\
- %WINDIR%\Tasks
- %WINDIR%\System32\Tasks
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
- %TEMP%
Step 7: Look for the malicious files created by Torpig and delete them.
Step 8: Close the File Explorer.
The next step below is not recommended for you if you don’t know how to navigate the Registry Editor. Making registry changes can highly impact your computer. So it is highly advised to use PC Cleaner Pro instead to get rid of the entries that the Trojan has created. PC Cleaner Pro is a trusted program that helps in improving your computer’s overall performance by repairing any registry issues as well as optimizes your system. If you are not familiar with the Windows Registry skip to Step 14 onwards. However, if you are well-versed in making registry adjustments, then you can proceed to step 10.
Step 9: Open the Registry Editor, to do so, tap Win + R and type in regedit and then press enter.

Step 10: Go to the following locations and delete all the registry keys and sub-keys created by Torpig.
- HKEY_CURRENT_USER\Software\
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step 11: Close the Registry Editor
Step 12: Launch Google Chrome.
Step 13: Empty your Recycle Bin.
Once you got rid of Torpig from your PC, follow the advanced guide below to get rid of it’s the files it has created.
Perform a full system scan using SpyRemover Pro. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading the program. The installation will start automatically once a download is done.
- Click OK to launch it.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register the program to protect your computer from future threats.