What is Wannary 3.0 ransomware?
Wannacry 3.0 is the third version of the well-known and notorious Wannacy ransomware that has earned its fame because of the damage it has inflicted all over the globe. It has been a month since the first version came out and since users with outdated operating systems had experienced the full assault of this menace that really made them want to cry.
Just like its predecessors, Wannacry 3.0 also exploited the EternalBlue vulnerability in the SMB servers which was leaked by Shadow Brokers, who stole the original tool from the National Security Agency. However, unlike its older versions, its developers made sure to fix any flaws or loopholes so that Wannacry 3.0 won’t be easily terminated by a kill switch which is what happened to its previous versions. This nightmare in the making was developed for self-defense purposes, fully equipped to make sure it surpassed the nightmare that was Wannacry ransomware.
How does Wannacry 3.0 ransomware work?
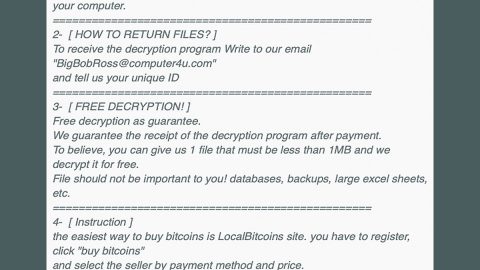
Once it infiltrates your computer, Wannacry 3.0 starts to encrypt your files such as your pictures, videos, audio files, documents, archives, and many more. During the encryption process it appends its file extension. Its encryption process does not take too long. Another thing to note is that Wannacry 3.0 uses a strong encryption algorithm to make it hard for its victims to decrypt the files, making it next to impossible to do. After that it displays its ransom note and demands hundreds of dollars worth in Bitcoins in exchange for the decryption key which is actually next to impossible to get even of you give the cyber criminals the money.
How does Wanncry 3.0 ransomware distributed?
Wannacry 3.0 can be obtained once you download an infected file from a spam email. Many users fell for this trick since cyber criminals have become quite wise in sending out spam emails with the infected attachment since they disguise the spam email as something that is an urgent email message or any other thing to make it look like an important message to lure users into downloading its attachments.
Eliminating the Wannacry 3.0 ransomware:
The first step below is not recommended for you if you don’t know how to navigate the Registry Editor. Making registry changes can highly impact your computer. So it is highly advised to use PC Cleaner Pro instead to get rid of the entries that Wannacry 3.0 ransomware created. So if you are not familiar with the Windows Registry skip to Step 5 onwards.
However, if you are well-versed in making registry adjustments, then you can proceed to step 1.
Step 1: Open the Registry Editor, to do so, tap Win + R and type in regedit and then press enter.
Step 2: Navigate to the path below:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
Step 3: Delete the any suspicious registry value.
Step 4: Close the Registry Editor.
Step 5: Open the File Explorer by pressing the Windows key + E.
Step 6: Go to the directories listed below and delete everything in it. Or other directories you might have saved the infected file related to the Wannacry 3.0 ransomware.
-
%USERPROFILE%\Downloads
-
%USERPROFILE%\Desktop
-
%TEMP%
Step 7: Under Desktop, delete its ransom note.
Step 8: Empty your Recycle Bin.
Step 9: Try to decrypt your encrypted files using the Windows Previous Versions feature.
Keep in mind that decrypting your encrypted files using Windows’ Previous Versions feature will only be effective if the Wannacry 3.0 ransomware hasn’t deleted their shadow copies. But still, this is one of the safest and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

Step 10: Disable the SMB Windows feature to prevent Wannacry 3.0 and other threats from infecting your computer again. To do that, follow these steps:
-
Click on the Windows button and type Windows features.
-
Select the entry Turn Windows features on or off.
-
Look for SMB 1.0/CIFS File Sharing support
- Remove the checkmark.
- The system will ask you to reboot the device in order for the changes to take effect.
Follow the continued advanced steps below to ensure the removal of the Wannacry 3.0 ransomware:
Perform a full system scan using SpyRemover Pro. To do so, follow these steps:
-
Turn on your computer. If it’s already on, you have to reboot it.
-
After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
-
To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit Enter.
-
Windows will now load the Safe Mode with Networking.
-
If done correctly, the Windows Run Box will show up.
-
Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
-
A dialog box will be displayed by Internet Explorer. Click Run to begin downloading SpyRemover Pro. Installation will start automatically once download is done.
-
Click OK to launch SpyRemover Pro.
-
Run SpyRemover Pro and perform a full system scan.
-
Register SpyRemover Pro to protect your computer from future threats.