What is Helponyon.info Ransomware?

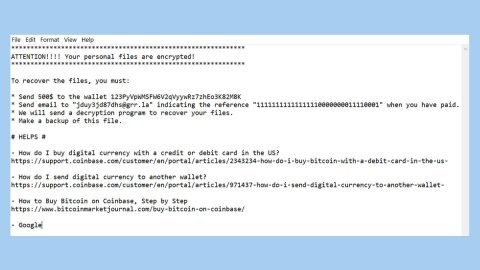
[email protected] ransomware is another member from the BTCWare family which are typically malicious programs that encrypts files. This crypto-malware continues the harmful tasks of Onion and OnionLock ransomware viruses that encrypts files using sophisticated cryptography and complicated algorithm and appends [[email protected]].master file extension to each of the targeted document, text, audio, video, image and other files. Once data is locked with strong cipher, the ransomware then sends or leaves a ransom-demanding message on the infected computer’s system. It contains the instructions on how to restore files are presented in “!#_RESTORE_FILES_#!” file. Then the victims are set and told that they have 36 hours to contact cyber criminals and learn how much Bitcoins they need to transfer for the decryption key once payment has been made. Authors of the [email protected] ransomware virus rush people to send an email by saying that the size or amount of the ransom depends on their speed, so, the longer they wait, the more money they have to pay. Stated in the ransom note that after the deadline, the decryption key will be deleted permanently thus there would be no chance to recover their files if they ignore or delay the payment. But actually, these talks are nothing else but psychological terror which means it’s only a threat and they might be remained unharmed. Thus, you should not do what they demand and don’t listen to them and rather scan the computer with a reputable malware removal program because it will help eliminate the [email protected] completely.
Hackers prove their credibility by allow decrypting three files for free. Basically, the victims can send files encrypted by [email protected] ransomware that are less than 1MB and that do not contain valuable information, and hackers send back decrypted data. However, having business with criminals is definitely not recommended. Possibly, these three files might be the only one that you get back from the hackers. Once you pay the ransom amount demanded, cyber criminals might disappear and forget their deal. Take note that the main purpose of this cyber infection is to trick people and swindle the money from innocent users. Thus, paying attention to [email protected] removal is highly advised and later try alternative data recovery methods. Also remember not to believe that attempting to recover your files through using third-party software will lead to data loss. It’s simply a cheap trick to persuade people to follow hackers’ orders.
How is the ransomware virus spread?
One of the many ways how [email protected] ransomware virus spreads is mainly through malicious spam emails. Usually, the cyber criminals apply social engineering techniques to trick and convince people into opening the infected document or visit a malicious website. Phishing emails often look like sent from delivery services, banks, retailers or even governmental institutions to make it seem trustworthy or reputable, thus, users can be easily misled by this trick and click on a harmful content. Often, the attached Word or PDF document is faked and may download malware payload on the system. Other than that, the [email protected] hijack might also occur when a user inadvertently clicks on a malware-laden ad. The problem is that safe and malicious ads usually look the same so you can’t be sure which one is safe and which one is not. In fact, infected ads might be delivered on the legitimate websites. Without doubts, catching ransomware in high-risk websites is higher thaMoreover, [email protected] ransomware virus might also be distributed using rogue software updates and downloads, and this malware might be distributed on various P2P networks, file-sharing sites, and torrents. In short, you should also stay away from these places and download software from publisher’s site.
How to Maually Remove Helponyon.info Ransomware?
Delete Helponyon.info Ransomware
- Press Ctrl+Shift+Esc and click Processes.
- Kill (right-click on the process and select End Process/End task) processes of Helponyon.info.
- Open the Windows Explorer (tap Win+E).
- Type %APPDATA% in the address bar and press Enter.
- Delete !#_RESTORE_FILES_#!.inf.
- Remove all suspicious files from %TEMP%, %USERPROFILE%\Downloads, and %USERPROFILE%\Desktop.
- Close the Windows Explorer.
- Tap Win+R, enter regedit.exe, and click OK.
- Move to HKCU\Software\Microsoft\Windows\CurrentVersion\Run.
- Right-click on the DECRYPTINFO Value and select Delete.
- Empty Recycle bin and reboot your PC.
How to remove [email protected] ransomware virus from the computer using professional software
To help you with the [email protected] removal, you have to invest into reputable anti-malware program. This dangerous cyber threat might have installed numerous malicious files and affected legitimate system processes which definitely and importantly needs to get fixed and a proper treatment. We highly recommend using reliable removal tools such as SpyRemover Pro for virus elimination procedure and also PC Cleaner Pro to clean you computer system. For instance, if you cannot install or update these programs, you restart the computer to the Safe Mode with Networking. Furthermore, scan the system using the removal tool and remove [email protected] ransomware several times.
For non-techie:
Undesirable applications which secretly work in the background on users’ computers exist too and sometimes slows down the PC’s performance, so we cannot guarantee that your PC is clean after you have manually deleted Helponyon.info Ransomware. Theoretically, other malicious applications might be working on your PC without your knowledge as well or being hidden to the core that it’s difficult to detect by the scanners – they could have entered together with the ransomware infection. Since they might be located anywhere, we believe it would be easier to automatically detect and erase them using an automated tool.
These instructions indicate how to get rid of Helponyon.info Ransomware automatically. The instructions need to be applied on the infected computer.
- Turn the infected computer on. If it is turned on, restart it.
- When BIOS screen disappears after the reboot, tap F8 key repeatedly. Advanced Options menu will show up. If Windows logo appears, reboot the PC and try pressing F8 again.
- When you access Advanced Options menu, use arrow keys to navigate and choose Safe Mode with Networking. Press Enter to access the mode.

4. Wait for Windows to load Safe Mode with Networking.
5. Press and hold the Windows key and then press R key.


6. If you have pressed both keys correctly, Windows Run Box will pop up.
7.Type the following into the Open box:
explorer https://www.fixmypcfree.com/removal
*Note, that there has to be a single space gap in between iexplore and http. Click OK.
8. Internet Explorer will open and a download dialog bar will appear at the bottom of your screen. Click Run to begin the installation automatically once SpyHunter is downloaded.

9. Click OK if your system asks whether you want to run SpyHunter software.
10. Run SpyHunter and perform a full system scan.
11. Once all the malicious infections are detected, click Fix Threats. SpyHunter will ask you to register the software.
12. By registering SpyHunter you will also be able to protect your computer from other potential threats. Once you have registered the program, the malware will be removed. Reboot your PC to fully implement the malware removal procedure.
“use a one click solution like SpyRemover Pro”