What is Asasin ransomware? And how does it carry out its attack?
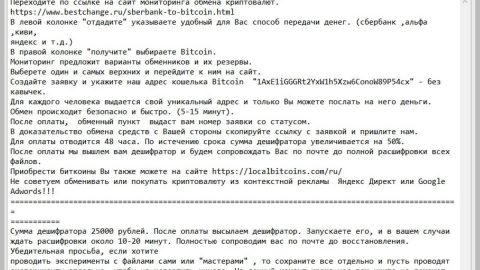
Asasin ransomware is another variant of the high-risk Locky ransomware. This new variant was identified just this month of October 2017 and has been spreading through spam emails as a fake invoice. Once the fake invoice is downloaded and opened in the computer, it will start its infiltration in the system by installing the Asasin ransomware. It then begin its attack by encrypting computer’s data using two encrypting algorithms – the RSA 2048 and the AES 128 ciphers. During the encryption process, Asasin ransomware renames the compromised files by adding 36-character strings and appending the asasin file extension. Following data encryption, the crypto-malware drops three additional malicious files into the system such as the asasin.bmp, asasin-5eac.htm, and asasin.htm. The BMP file is set as the computer’s new wallpaper background while the two htm files provides information as to what happened to the encrypted data – these two files are placed on the desktop and also gives detailed instructions on how to recover the encrypted files and pay the ransom – both of these files contain the following ransom note:
“!!! IMPORTANT INFORMATION !!!!
All of your files are encrypted with RSA-2048 and AES-128 ciphers. More information about the RSA and AES can be found here: hxxp://en.wikipedia.org/wiki/RSAicryptosysteml hxxp://en.wikipedia.org/wiki/Advanced_Encryption_Standard
Decrypting of your files is only possible with the private key and decrypt program, which is on our secret server. To receive your private key follow one of the links:
If all of this addresses are not available, follow these steps: 1. Download and install Tor Browser: hxxps://www.torproject.org/download/download-easy.html 2. After a successful installation, run the browser and wait for initialization. 3. Type in the address bar: g46mbrrzpfszonuk.onion/GPZ9PT8ABFEUGKAJ 4. Follow the instructions on the site.
!!! Your personal identification ID: GPZ9PT8ABFEUGKAJ !!!”
As you can see, Asasin ransomware demands 0.25 Bitcoins which is equal to more than a thousand dollars. And sad to say that the ransom note does not lie – there is no other way to restore the encrypted files unless you have a decryption key. However, that shouldn’t be reason enough for you to give in and pay the ransom as these crooks might only trick you some more and you end up losing a big chunk of money for nothing. As of now, there is no free decryption tool developed yet, so the best thing you can do is to use any backup copies of the affected files and if you don’t have them, then you’re best option is to wait as you can’t use the Shadow Volume Copies of the files since the ransomware has deleted them.
How does Asasin ransomware proliferate?
As mentioned earlier, Asasin ransomware spreads via malicious spam email campaigns. In the email, the attackers attached a malicious file disguising as an invoice in a PDF file and is sent from [email protected]. Based on the email address, the attackers seem to be using a web and mobile e-signature company, RightSignature. The crooks also put “Document invoice _95649_sign_and_return.pdf is complete” as the subject of the email. There is no wonder a lot of users were tricked into downloading the infected attachment as the malevolent attachment is not visible to users. Cyber criminals these days are now getting better in disguising their malicious files just like with Asasin ransomware so you have to be careful in opening any email especially the one which came from unknown senders. Check the body of the email as one of the telltale signs that the email is sent by crooks is poor grammar and wrong spellings. Also, it would be better if you scan any downloaded attachment before you open them. In addition, keeping your system and antivirus programs updated would greatly help in detecting malware and preventing these kinds of attacks.
Obliterate Asasin ransomware using the step by step guide below.
Step 1: Tap Ctrl + Shift + Esc to open the Task Manger.

Step 2: Once you’ve opened the Task Manager, go to the Processes tab and look for Asasin’ processes and other suspicious ones and right click on them and select End Task to end their processes.

Step 3: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.

Step 4: Look for Asasin ransomware or any suspicious program and then Uninstall it/them.

Step 5: Tap the Win + E keys to open the File Explorer.
Step 6: Navigate to the following locations below.
- %TEMP%
- %APPDATA%
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
Step 7: After opening the directories listed above, look for the following malicious files and delete them:
- bmp;
- asasin-5eac.htm;
- htm.
Step 8: Close the File Explorer. Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use PC Cleaner Pro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step 9: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 10: Navigate to the following paths:
- HKCU\Software\Classes\.PNR
- HKCU\Software\Classes\Asasin
Step 11: Delete the registry keys and sub-keys created by Asasin ransomware.
Step 12: Close the Registry Editor.
Step 13: Empty your Recycle Bin.
To make sure that nothing is left behind and that the Asasin is completely removed, use the following antivirus program. To use it, refer to the instructions below.
Perform a full system scan using SpyRemover Pro. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOSscreen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Optionuse the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Boxwill show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading the program. Installation will start automatically once download is done.
- Click OK to launch it.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register the program to protect your computer from future threats.