What is TeslaWare ransomware?
TeslaWare is a new virus infection that functions as a file-encrypting threat. Take note that the TeslaWare ransomware is not in any way related to the famous electric automobile company, Tesla. It may have taken the automobile company’s name to trick users into believing that the company is the one behind this ransomware. The TeslaWare is quite similar to other ransomware since it also uses the AES 256 algorithm to encrypt your computer’s files. During the encryption, it appends its files extension, .tesla to all your files. It usually targets these kinds of files extensions from your computer: .sys, .dll, .exe, .tesla, .lnk.

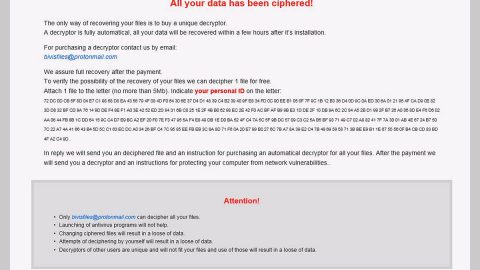
Once the TeslaWare is done with the encryption process, it drops its ransom note in the form of a window as you can see the illustration above, which contains the following message:
“All of your important files have been encrypted.
To decrypt them you need to obtain the private key from us.
We are the only who can provide you the key,so don’t try to recover the files by yourself,it will only make the situation worse for you.
To get this key you have to send 100$ worth of bitcoins to the address that you can see in the left.For more info please check the links
After payment,please paste the TX ID and press “Check”.If our system detected the payment as succesfull,your files will be decrypted and you will use your pc as nothing happened.
Send exactly 0.0133753 here:
[BITCOIN ADDRESS]”
Apart from the .sys, .dll, .exe, .tesla, .lnk file extensions, the TeslaWare also targets multiple files from different location on your computer. Although the TeslWare uses the same algorithm like most ransomware, this ransomware can encrypt over 100 kinds of file types such as the common ones like, .png, .mp4, .doc, and .ppt. According to our researchers, once it infects your computer, it scans different computer directories such as your desktop, downloads, pictures, videos, music, templates and whole lot more for certain file types mentioned above. Another thing to take note is that this ransomware is programmed to identify different kinds of disk partitions. The number and names of the volumes highly depends on the user. While the partition names are scanned alphabetically.
Moreover, the TeslaWare has the ability to kill your Task Manager and Process Explorer. So once it kills your Task Manager, you won’t be able to get information or view the running processes in your computer. As for the Process Explorer, you will no longer have access to your DLL version issues and get information about the running windows applications in your computer. And if you think that paying the ransom would be the easiest way out, then you’re wrong. Even if you can’t access both Task Manager and Process Explorer to get rid of the TeslaWare, don’t lose hope for this article will provide you alternative solutions to eliminate the ransomware. And besides, our researchers have tried the TeslaWre’s decryption key which is Z85tp2sWTW1LQGvT2CTOUgaKHDWNWY=== but it did not work after the conducted tests. So paying the ransom is a big no, no.
How is TeslaWare ransomware distributed?
As per our researchers, the TeslaWare was detected as Gen:Variant.MSILPerseus.84936, Trojan.MSILPerseus.D14BC8, and Gen:Variant.MSILPerseus.84936 trojan which could mean that this ransomware is distributed using several techniques, such as corrupted torrent files, useless or “abandoned” applications as well as the good old distribution method; spam emails.
Follow the steps below to get rid of the TeslaWare ransomware:
The first step below is not recommended for you if you don’t know how to navigate the Registry Editor. Making registry changes can highly impact your computer. So it is highly advised to use PC Cleaner Pro instead to get rid of the entries that TeslaWare Ransomware created. So if you are not familiar with the Windows Registry skip to Step 5 onwards.

However, if you are well-versed in making registry adjustments, then you can proceed to step 1.
Step 1: Open the Registry Editor, to do so, tap Win + R and type in regedit and then press enter.
Step 2: Navigate to the path below:
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run|MicrosoftAudioDriver
Step 3: Delete the registry value named MicrosoftAudioDriver.
Step 4: Close the Registry Editor.
Step 5: Open the File Explorer by pressing the Windows key + E.
Step 6: Go to the directories listed below and delete everything in it. Or other directories you might have saved the infected file related to the TeslaWare Ransomware.
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
- %TEMP%
Step 7: Under Desktop, delete the text file, READ_ME.txt.
Step 8: Empty your Recycle Bin.
Follow the continued advanced steps below to ensure the removal of the TeslaWare Ransomware:
Step 9: Perform a full system scan using SpyRemover Pro. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the Safe Mode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading SpyRemover Pro. Installation will start automatically once download is done.
- Click OK to launch SpyRemover Pro.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register SpyRemover Pro to protect your computer from future threats.
Step 10: Try to decrypt your encrypted files using the Windows Previous Versions feature.
Keep in mind that decrypting your encrypted files using Windows’ Previous Versions feature will only be effective if the TeslaWare Ransomware hasn’t deleted their shadow copies. But still, this is one of the safest and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.