What is CryptoGod ransomware? And how does it implement its attack?
CryptoGod ransomware is a file-encrypting virus which is created based on the HiddenTear ransomware – an open source platform that was developed initially for educational purposes but was exploited by cybercriminals. At the time of writing, it seems that the current samples released from this crypto-malware are test versions but it could be updated any time soon.
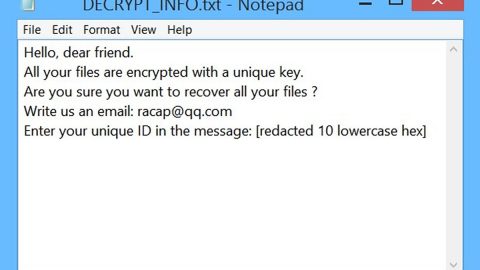
According to security experts, CryptoGod ransomware was created by a hacker named “Patrizio Napoli” as his signature was found in the ransomware’s code. Since this ransomware is still under development, it does not feature any modules on its attack yet. However, this ransomware must still not be taken lightly as it could be updated by its creator. Once it encrypts a targeted machine, it will start to encrypt targeted files using the AES encryption algorithm. It may target user-generated files like archives, images, music, documents, videos, database and many more. The compromised files are then appended with the .locked extension. After it marks its encrypted files, it opens a lock screen instance which contains the following message:
“I TUOI FILE PERSONALI STANNO PER ESSERE
CANCELLATI. LE TUE FOTO, VIDEO, DOCUMENTI
ETC…
MA NON PREOCCUPARTI! SUCCEDERA SOLO SE
NON SEGUL LE REGOLE.
HO GIA CRIPTATO I TUOI FILE, IN MODO CHE TU
NON POSSA ACCEDRVI. OGNI ORA SELEZIONERO
UNO DI LORO E LO CANCELLERO IN MODO
PERMANENTE, DOPO 24 ORE LI CANCELLERO
TUTTI, QUENDI NEMMENO IO SARO PIU IN GRADO
DI RECUPERARLI.
SONO L’UNICO IN GRADO DI DECRIPTARE I TUOI
DATI…
ORA, GUARDA I TUOI FILE, NON POTRAL
DECRTIPTARLI SENZA PAGARE.
LA CIFRA DA PAGARE PER RIAVERE I FILE E DID
300€ IN CODICI PAYSAFECARD.
PUOI INSERIRE DIRETTAMENTE QUI SOTTO I TUOI
CODICI PAYSAFECARD, IL NOME DEL TUO PC ED
UNA TUA E-MAIL PER INVIARLE IL CODICE DI
DECRIPTAZIONE DEI FILE.”
Here’s an English translation of the ransom note via Google Translate:
“YOUR PERSONAL FILES ARE TO BE
DELETED. YOUR PHOTOS, VIDEOS, DOCUMENTS
ETC…
BUT DO NOT WORRY! SUCCEDERA ONLY IF
DO NOT SIDE THE RULES.
I HAVE CRYPTED YOUR FILES, SO THAT YOU
CAN NOT ACCEPT. EVERY HOUR SELECTED
ONE OF THEM AND CANCEL IT IN A WAY
PERMANENT, AFTER 24 HOURS CLEARLY
EVERYONE, IM NOT EVEN MORE ABLE
TO RECOVER THEM.
I AM THE ONLY ABLE TO DECREASE YOURS
DATA…
NOW, WATCH YOUR FILES, DO NOT MAKE IT
DECREASE WITHOUT PAYING.
THE NUMBERS TO BE PAID TO REACH THE FILES AND DID
€ 300 IN PAYSAFECARD CODES.
YOU CAN INSERT DIRECTLY HERE UNDER YOURS
CODES PAYSAFECARD, THE NAME OF YOUR PC ED
YOUR E-MAIL TO SEND THE CODE OF
DECREASING FILES.”
How does CryptoGod ransomware spread online?
Although CryptoGod ransomware is not being actively distributed yet, if its developer decide to update it and spread it online, it might be via malicious spam email campaigns so you need to be careful in opening emails from your inbox as crooks tend to disguise their malware-laden emails to lure users into opening them and downloading the attached file.
Terminating CryptoGod ransomware from your computer wouldn’t be easy so you need to carefully follow each one of the removal steps given below.
Step 1: Tap Ctrl + Shift + Esc keys to launch the Task Manager.
Step 2: Go to Processes and look for the malicious process of CryptoGod ransomware named CryptoGod.exe and then right click on it and select End Process or End Task.

Step 3: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.
Step 4: Look for dubious programs that might be related to CryptoGod ransomware and then Uninstall it/them.

Step 5: Tap Win + E to launch File Explorer.
Step 6: After opening File Explorer, navigate to the following directories below and look for CryptoGod ransomware’s malicious components such as [random].exe, CryptoGod.exe, and LEGGIMI.txt and other suspicious-looking files and then remove them all.
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- C:\ProgramData\local\
Step 7: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use [product-name], this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then, by all means, go on to the next steps.
Step 8: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 9: Navigate to the listed paths below and look for the registry keys and sub-keys created by CryptoGod ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step 10: Delete the registry keys and sub-keys created by CryptoGod ransomware.
Step 11: Close the Registry Editor.
Step 12: Empty your Recycle Bin.
Try to recover your encrypted files using the Shadow Volume copies
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if CryptoGod ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

Once you’re done executing the steps given above, you need to continue the removal process of CryptoGod ransomware using a reliable program like [product-name]. How? Follow the advanced removal steps below.
Perform a full system scan using [product-code]. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in the URL address, [product-url] in the Run dialog box and then tap Enter or click OK.
- After that, it will download the program. Wait for the download to finish and then open the launcher to install the program.
- Once the installation process is completed, run [product-code] to perform a full system scan.
- After the scan is completed click the “Fix, Clean & Optimize Now”button.