What is Naampa ransomware? And how does it work?
Naampa ransomware is file-encoding virus makes use of RSA 2048 encryption algorithm in encrypting the targeted files. It appends .crptd file extension to each of your system’s database, archive files, videos, mp3, mp4, text files and other kinds of files. After it executes the encryption, it drops a file named README !.jpg which is the ransom note written in Russian and contains the following text:
‘Ваши файлы зашифрованы с использованием алгоритма RSA-2048.
Если хотите их вернуть отправьте один из зашифрованных файлов и файл key.res на e-mail:
[email protected]
Если вы не получили ответа в течение суток или письмо возвращается с ошибкой то скачайте с сайта www.torproject.com браузер TOR и с его помощью зайдите на сайт
hxxp://n3r2kuzhw2h7x6j5.onion – там будет указан действующий почтовый ящик.
Попытки самостоятельного восстановления файлов могут безвозвратно их испортить!’
Ransom note translated to English:
‘Your files are encrypted using the RSA-2048 algorithm.
If you want to recover them, send one of the encrypted files and key.res file to e-mail:
[email protected]
If you do not receive a reply within 24 hours or the letter is returned with an error, then download from the site www.torproject[.]com browser TOR and go to the site
hxxp://n3r2kuzhw2h7x6j5.onion – there will be specified a valid mailbox.
Attempts to repair the files yourself can irreversibly damage them!’
According to our researchers, Naampa ransomware is related to Unlock92 ransomware that attacked a big number of Russian users way back 2016. Naampa is developed using the C# programming language. This ransomware spreads using two malicious executable files: naampa.exe and mmspert.exe. Both of these malicious executable files are responsible in carrying out the attacks and tasks on the infected computer.
The cyber criminals behind Naampa not only encrypts your important files but can also do some damage on your computer since it modifies entries on your Windows Registry. This is a dangerous thing since your Registry is an essential part of your computer system and any unnecessary changes or mistakes can greatly affect your computer. It might install malicious files to execute harmful tasks. It creates and places the modified components in the Registry in these directories:
- %USERPROFILE%\Documents\– -README– -!.jpg
- %USERPROFILE%\Documents\key.res
Even if Naampa ransomware is a grave threat to both your files and computer system, you still shouldn’t resort to paying the ransom since most cyber criminals tend to ignore the victims after receiving the payment. And besides there are many alternative solutions you can try to get rid of this threat such as the removal guide below.
How is Naampa ransomware distributed?
Naampa ransomware uses corrupted .docx files which are macro-enabled. These macro-enabled .docx files serve as an installer for Naampa to start the infiltration. Macro scripts are intended to help users in automating the same tasks and interpreted by Windows as direct commands from the users which is taken advantage by the crooks behind ransomware infections. The corrupted .docx files are sent out wave after wave through spam emails. Once the installer is launched, the system receives commands to connect to a remote server and download several encrypted packages.
Furthermore, Naampa ransomware also uses two malicious executable files like mentioned earlier which are naampa.exe and mmspert.exe. These files are also sent out through spam emails. So there is no wonder that this ransomware has infected big numbers of users due to the tricks it uses in carrying out its attack.
To terminate Naampa ransomware and its tasks, follow the removal instructions below:
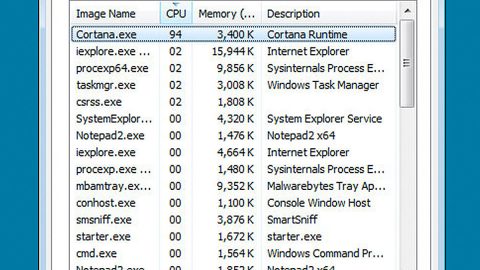
Step 1: Open the Windows Task Manager by pressing Ctrl + Shift + Esc at the same time. Proceed to the Processes tab and look for naampa.exe or mmspert.exe and other suspicious processes that can be related to the Naampa Ransomware.

Right-click on the processes, then click Open File Location and scan them using a powerful and trusted antivirus like SpyRemover Pro. After opening their folders, end their processes and delete their folders. If the virus scanner fails to detect something that you know is suspicious, don’t hesitate to delete it.
Step 2: Open Control Panel by pressing Start key + R to launch Run and type appwiz.cpl in the search box and click OK.

Look Naampa ransomware or any peculiar program and then Uninstall it.

Step 3: Hold down Windows + E keys simultaneously to open File Explorer.
Step 4: Go to the directories listed below and delete everything in it. Or other directories you might have saved the file related to Naampa ransomware.
- %AppData%
- %Roaming%
- %Local%
- %LocalLow%
- %Temp%.
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
Step 5: Look for corrupted .docx file as well as the naampa.exe and mmspert.exe malicious executable files.
Step 6: Go to your desktop and look for README !.jpg and remove it.
The next step below is not recommended for you if you don’t know how to navigate the Registry Editor. Making registry changes can highly impact your computer. So it is highly advised to use PC Cleaner Pro instead to get rid of the entries that Naampa ransomware created. So if you are not familiar with the Windows Registry skip to Step 11 onwards.

However, if you are well-versed in making registry adjustments, then you can proceed to step 7.
Step 7: Open the Registry Editor, to do so, tap Win + R and type in regedit and then press enter.
Step 8: Navigate to the path below:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
Step 9: Delete the any suspicious registry value.
Step 10: Close the Registry Editor.
Step 11: Empty the Recycle Bin.
Step 12: Try to recover your encrypted files.
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if the Naampa Ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

Follow the continued advanced steps below to ensure the removal of the Naampa ransomware:
Perform a full system scan using SpyRemover Pro. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the Safe Mode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading SpyRemover Pro. Installation will start automatically once download is done.
- Click OK to launch SpyRemover Pro.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register SpyRemover Pro to protect your computer from future threats.