What is QuasarRAT? And how does it function?
QuasarRAT or Quasar Remote Access is identified to be a Trojan virus and a highly modified version of an open source project which also goes by the name QuasarRAT created by a programmer called as “quasar” who has a page at Github.com/quasar/QuasarRAT. This program both have its clean and malicious versions which mainly differs on how they are packed and the presence of an obfuscation layer and manner of network communication. This program was used in targeted attacks on the government of the United States in early 2017. Recently, samples of this Trojan began surfacing this October along with reports of new attacks.
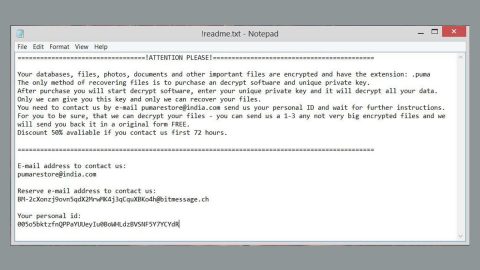
According to security experts, this Trojan-dropper is observed to extract a copy of the Downeks threat which was known for its attacks before. They also added that the Downeks Trojan-dropper connects to a hard-coded URL and downloads the main body of the Trojan. Once QuasarRAT is installed in the system, the attackers behind this Trojan will have access to all the information saved in the computer as well as the connected network data storage. This Trojan also has the ability to install third party programs – malicious ones included – and remove programs along with terminating system processes and take screenshots.
And if you think, that’s how worse this Trojan can get, you’re wrong. That is not the full extent that the remote user can do. Security experts added that this Trojan could even download other files and make changes in the Registry, open remote desktop connections, collect personal information like passwords, load web pages, issue to both the keyboard and the mouse. It is also found that QuasarRAT exploits vulnerabilities of client-server communication which could allow the crooks behind this Trojan to launch a counterattack and install a copy of QuasarRAT on the Command and Control servers used by the first attacker potentially. Researchers also advised against removing QuasarRAT manually unless you are well-versed in these kinds of things and suggested using a top-rated antivirus program like SpyRemover Pro.
How is QuasarRAT disseminated online?
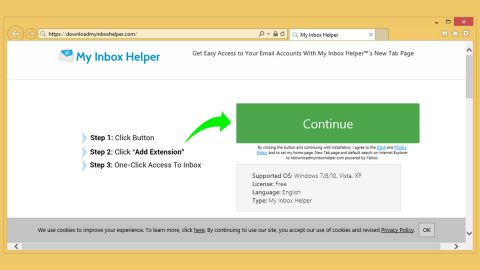
QuasarRAT Trojan is promoted as a Remote Administration Tool or RAT for server admins and cyber security managers in the government as well as private sectors. Aside from that, users can get infected by this Trojan when they open an attachment to a spear phishing email. Most of the contents of QuasarRAT’s malicious emails contain documents titled as “Scanned Document”, “Audio Recording”, “Presentation” and other similar names. These are actually fake documents which may have double extension i.e., “Scanned Document.doc.exe”. A lot of users were tricked into opening these corrupted attachments as the crooks disguised the documents with icons to seemingly safe files which are usually associated with Microsoft Office. When users open this kind of attachment, a User Account Control pops up on the screen instead of opening application from Microsoft Office.
Step 1: Tap Ctrl + Shift + Esc keys to pull up the Task Manager.
Step 2: Go to the Process tab, look for QuasarRAT’s process and click End Task or End Process to end it.

Step 3: Close the Task Manager and then open Control Panel by pressing Win + R to launch Run and type appwiz.cpl in the search box and click OK.

Step 4: Look for QuasarRAT or any malicious program and then Uninstall it.

Step 5: Tap the Win + E keys to open File Explorer.
Step 6: Go to the directories listed below and then look for the corrupted files created by QuasarRAT and delete all of them.
- %APPDATA%\Microsoft
- %APPDATA%\system
- %WINDIR%\SysWOW64\SubDir
- %PROGRAMFILES(x86)%\[random characters]
The next step below is not recommended for you if you don’t know how to navigate the Registry Editor. Making registry changes can highly impact your computer. So it is highly advised to use PC Cleaner Pro instead to get rid of the entries that QuasarRAT created. So if you are not familiar with the Windows Registry skip to Step 9 onwards.

However, if you are well-versed in making registry adjustments, then you can proceed to step 7.
Step 7: Open the Registry Editor, to do so, tap Win + R and type in regedit and then press enter.
Step 8: Navigate to the following path:
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
Step 9: Delete any registry keys or sub-keys created by the Trojan.
Step 10: Close the Registry Editor and empty the Recycle Bin.
To make sure that nothing is left behind and that the QuasarRAT is completely removed, use the following antivirus program. To do so, refer to the instructions below.
Perform a full system scan using SpyRemover Pro. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOSscreen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Optionuse the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Boxwill show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading the program. Installation will start automatically once download is done.
- Click OK to launch it.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register the program to protect your computer from future threats.