What is Unlock92 2.0 ransomware? And how does it carry out its attack?
Unlock92 2.0 ransomware is a file-encrypting malware that appears to target Russian-speaking users. This ransomware threat was first released in 2016 but was once again spotted out in the wild recently. It uses the RSA 2048 encryption algorithm in locking its targeted files. Once its malicious payload is executed, it will begin to carry out its attack by modifying system files to repress any program installed in the computer from interfering with its attack. Aside from that, it also creates and alters some Registry entries in order to run on every system boot. After these modifications are applied, Unlock92 2.0 ransomware will start to encrypt files with specific formats like audio files, images, documents, database, and many more. Most of the files it targets are user-generated which means that it encrypts users’ important data. It appends the .CRRRT, .CCCRRRPPP or .cdrpt extensions once it finishes encrypting files.
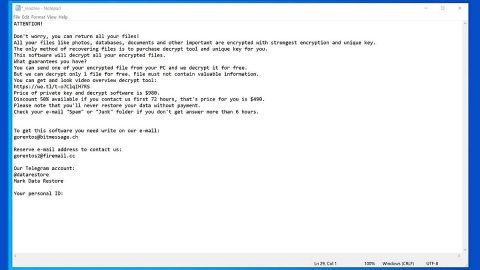
After data encryption, Unlock92 2.0 ransomware changes the desktop wallpaper of the infected PC with an image file named “ORID.jpg”. This image contains the ransom note written in Russian that states:
“Ваши файлы зашифрованы с использованием криптостойкого алгоритма RSA-2048.
Если хотите их вернуть отправьте один из зашифрованных файлов и файл keyvalue.bin на e-mail: [email protected]
Если вы не получили ответа в течение суток то скачайте с сайта www.torproject.con браузер TOR и с его помощью зайдите на сайт:
http://fnjmegsn7tbrrnkl.onion – там будет указан действующий почтовый ящик. Без браузера TOR зайти на этот сайт невозможно.
Попытки самостоятельного восстановления файлов могут безвозвратно их испортить!”
Here’s the English translation of the ransom note:
“Your files are encrypted using the RSA-2048 algorithm.
If you want to return them, send one of the encrypted files and key.res file to e-mail:
[email protected]
If you do not receive a reply within 24 hours or the letter is returned with an error, then download from the site www.torproject.com browser TOR and with his help go to the site
n3r2kuzhw2h7x6j5.onion – there will be specified a valid mailbox.
Attempts to repair files yourself can irrevocably ruin them!”
Cybercriminals behind this ransomware threat urge victims to contact the email address, [email protected] and send one encrypted file and to wait for their response. Victims are also asked to download the TOR browser to access specific websites. If you are one of the unlucky victims of this crypto-virus, you must not do any of these things as it will only get you into a further mess and end up losing money over nothing. The best way to deal with this kind of threat is by removing it from the infected system right away and use alternative ways to restore encrypted files.
How does Unlock92 2.0 ransomware proliferate?
Unlock92 2.0 ransomware proliferate using malicious spam email campaigns where its malicious payload is attached. Once this malicious payload is downloaded, it will launch Unlock92 2.0 ransomware into the system. This is why opening emails from dubious senders is not recommended and that you must delete them right away instead of opening them.
Use the removal guide prepared below in terminating Unlock92 2.0 ransomware from your computer.
Step 1: Open Windows Task Manager by pressing Ctrl + Shift + Esc at the same time.

Step 2: Go to both the Application and Processes tabs and look for any suspicious applications and processes affiliated to Unlock92 2.0 ransomware and then kill them.

Step 3: Open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.

Step 4: Look for Unlock92 2.0 ransomware or any suspicious program and then uninstall it/them.

Step 5: Hold down Windows + E keys simultaneously to open File Explorer.
Step 6: Navigate to the following directories:
- %USERPROFILE%\Desktop
- %USERPROFILE%\AppData\Local\Temp
- %USERPROFILE%\downloads
- %TEMP%
Step 7: Look for the malicious files created by the ransomware like the malicious macro-enabled document you’ve downloaded recently as well as the file named “ORID.jpg” and then delete them all and then close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use an efficient program like [product-name], this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then, by all means, go on to the next steps.
Step 8: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 9: Navigate to the following registry paths:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Authentication\LogonUI\Background
- HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\Personalization
- HKEY_CURRENT_USER\Control Panel\Desktop\ScreenSaveTimeOut
- HKEY_CURRENT_USER\Control Panel\Desktop
Step 10: Under the paths listed above, look for registry values created by Unlock92 2.0 ransomware and delete it.
Step 11: Close the Registry Editor
Step 12: Empty all the contents of Recycle Bin.
Try to recover your encrypted files using the Shadow Volume copies
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if Unlock92 2.0 ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

After you’ve covered the steps provided above, you need to continue the removal process of Unlock92 2.0 ransomware with the help of a reliable program like [product-name]. How? Follow the advanced removal steps below.
Perform a full system scan using [product-code]. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in the URL address, [product-url] in the Run dialog box and then tap Enter or click OK.
- After that, it will download the program. Wait for the download to finish and then open the launcher to install the program.
- Once the installation process is completed, run [product-code] to perform a full system scan.