Lenovo is the world’s largest PC maker. Today, Lenovo is also the world’s most controversial PC maker after it was caught pre-installing adware on desktop and laptop PCs.
Most PC makers install some form of adware: adware comes in the form of a free 30 day antivirus trial, or a backup software manager. But Lenovo’s adware is a lot more dangerous than that.
Lenovo’s adware is called Superfish and it injects third-party advertisements onto Google Searches.
So when you Google something on a Lenovo computer, you might click on an advertisement thinking it’s a Google ad, only to be redirected to one of Lenovo – or Superfish’s – advertisement partners.
Lenovo doesn’t hide the fact that it installs Superfish on its computers: it just advertises its functions differently. Lenovo claims Superfish is “intended to help consumers find and discover products by analyzing images” on the internet.
When you see a product you like, but don’t know its name, you can use the Superfish visual search tool to identify that product or find similar products.
Complaints about the Lenovo adware started popping up last week across the internet and users are mad. After all, Lenovo is the world’s largest computer maker, so there are more than a few angry Lenovo users out there.
The adware itself is described as “like Google on steroids”. Yikes.
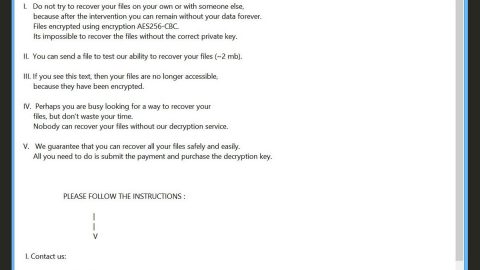
Superfish Can Issue Fake Security Certificates, Leaving Users Even More Vulnerable
Injecting unwanted advertisements into your Google searches is bad enough. But do you want to know what’s worse? Issuing fake security certificates to potentially malicious individuals.
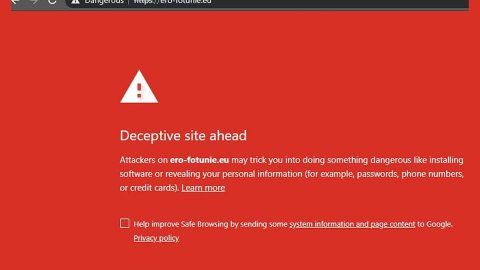
Superfish has the ability to issue its own security certificates. This lets is hijack SSL/TLS connections to websites – best known as a “man in the middle attack.”
During these attacks, users are tricked into thinking that a website has a real security certificate: it says it uses “HTTPS” and appears to be genuine. But in reality, that security certificate was issued by a third party, and that third party may or may not be malicious.
Are You a Lenovo User?
If you’re a Lenovo user, you can test whether or not Superfish is on your computer by typing Superfish into the Start menu. You should see a Superfish folder as well as a few different configuration files.
However, just because those files and folders are on your PC does not mean they’re active.
Lenovo issued a statement on the matter, saying the following three things:
1) Superfish has completely disabled server side interactions (since January) on all Lenovo products so that the product is no longer active. This disables Superfish for all products in market.
2) Lenovo stopped preloading the software in January.
3) We will not preload this software in the future.
If you believe Lenovo, then consumers are filled with fake outrage over a non-issue. If you’re naturally suspicious, however, Lenovo only yanked the software after it got caught. It fully admits to preinstalling the software on all Lenovo computers.
In any case, your computer should be Superfish-free. The big question is whether or not computer users can trust Lenovo going forward.