What is PayDay ransomware? And how does it implement its attack on the infected PC?
PayDay ransomware is a file-encrypting threat based on an open source platform, HiddenTear, which was first spotted way back in December 2016. However, at the beginning of this month in October, security experts noticed a new crypto-malware that appends .[]-id-.payday file extension on the targeted files. This recent cyber threat is said to be related to a new BTCWare variant which appends the .payday extension.
After it successfully infiltrated the affected computer, PayDay ransomware scans all the drive in the system for files to target. According to researchers, it encrypts the following file extensions:
.RAW, .TIF, .GIF, .PNG, .BMP, .3DM, .MAX, .ACCDB, .DB, .DBF, .MDB, .PDB, .SQL, .SAV, .SPV, .GRLE, .MLX, .SV5, .GAME, .SLOT, .DWG, .DXF, .C, .CPP, .CS, .H, .PHP, .ASP, .RB, .JAVA, .JAR, .CLASS, .AAF, .AEP, .AEPX, .PLB, .PREL, .PRPROJ, .AET, .PPJ, .PSD, .INDD, .INDL, .INDT, .INDB, .INX, .IDML, .PMD, .XQX, .XQX, .AI, .EPS, .PS, .SVG, .SWF, .FLA, .AS3, .AS, .TXT, .DOC, .DOT, .DOCX, .DOCM, .DOTX, .DOTM, .DOCB, .RTF, .WPD, .WPS, .MSG, .PDF, .XLS, .XLT, .XLM, .XLSX, .XLSM, .XLTX, .XLTM, .XLSB, .XLA, .XLAM, .XLL, .XLW, .PPT, .POT, .PPS, .PPTX, .PPTM, .POTX, .POTM, .PPAM, .PPSX, .PPSM, .SLDX, .SLDM, .WAV, .MP3, .AIF, .IFF, .M3U, .M4U, .MID, .MPA, .WMA, .RA, .AVI, .MOV, .MP4, .3GP, .MPEG, .3G2, .ASF, .ASX, .FLV, .MPG, .WMV, .VOB, .M3U8, .CSV, .EFX, .SDF, .VCF, .XML, .SES.
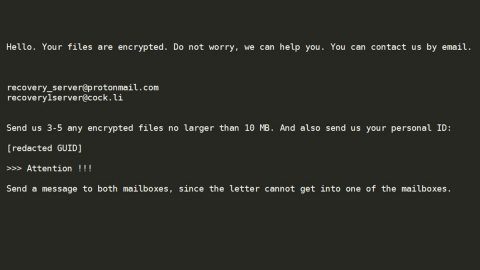
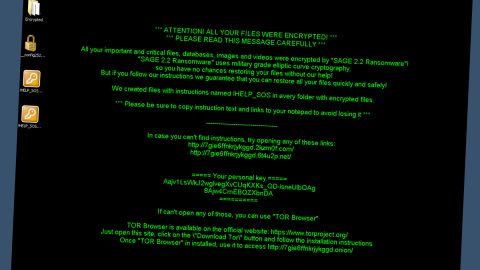
Once it finds the listed file extensions above, it encrypts them using the AES cryptography and appends the .sexy file extension on each one of them. And while it encrypts data, you might notice some system slowdowns. It then creates an html file named !!!!!ATENCAO!!!!!.html or !!!!!ATTENTION!!!!!.html that contains the following message:
“Seus arquivos foram Sequestrados!
os seus documentos, banco de dados, downloads, fotos e outros arquivos importantes foram criptografados utilizando o algoritmo com uma senha alfa-numérica de 150 caracteres gerada a partir deste computador e enviada para um servidor secreto na Internet onde somente eu tenho acesso.
O que fazer?
Para obter essa senha e descriptografar seus arquivos, você terá que pagar uma quantia de R$950,00 em BTC (BITCOIN). Para efetuar o pagamento e obter a senha, siga este pequeno manual:
- Crie uma carteira BTC aqui:
- Compre R$950,00 BTC com dinheiro em: localbitcoins.com
- Envie os BTCs comprados para o endereço: [34 random characters]
- Acompanhe a transferência em: blockchain.info/address/[34 random characters]
- Após o pagamento ser confirmado, envie-me um email requisitando a Senha: [email protected]
- Logo após, enviarei um arquivo compactado contento dois arquivos: um Decrypter em .exe e a Senha em um .txt
Importante:
- Ninguém pode te ajudar, a não ser eu!
- Você tem apenas 120 Horas (5 dias) para efetuar o pagamento, caso o contrario eu deletarei a senha.
- É inútil instalar/atualizar o software Anti Vírus, formatar o computador, fazer BO na delegacia, etc.
- Seus arquivos só poderão ser descriptografados depois do pagamento.
- A,pos você descriptografar seus arquivos, formate seu comutador, instale um bom Anti Vírus e tome mais cuidado onde clica”
Based on its ransom note, the users it mostly targets are Portuguese but that does not mean that it does not affect other users from other countries too as it uses a widely-used distribution method.
How does PayDay ransomware distribute its infection?
PayDay ransomware uses one of the common ways in distributing ransomware infection which is through malicious spam email campaigns.
Step 1: Open the Windows Task Manager by pressing Ctrl + Shift + Esc at the same time.
Step 2: Go to the Process tab, look for PayDay ransomware’s process and click End Task or End Process to end it.

Step 3: Open Control Panel by pressing Start key + R to launch Run and type appwiz.cpl in the search box and click OK.

Step 4: Look for PayDay ransomware or any malicious program and then Uninstall it.

Step 5: Tap the Win + E keys to open File Explorer.
Step 6: Go to the directories listed below and then look for the corrupted files such as !!!!!ATENCAO!!!!!.html and the malicious file it came with.
- %ALLUSERSPROFILE%\Application Data\Microsoft\Windows\Start Menu\Programs\Startup
- %ALLUSERSPROFILE%\Start Menu\Programs\Startup
- %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup
- %USERPROFILE%\Microsoft\Windows\Start Menu\Programs\Startup
- %ALLUSERSPROFILE%\Microsoft\Windows\Start Menu\Programs\Startup
- %USERPROFILE%\Desktop
The next step below is not recommended for you if you don’t know how to navigate the Registry Editor. Making registry changes can highly impact your computer. So it is highly advised to use PC Cleaner Pro instead to get rid of the entries that PayDay ransomware created. So if you are not familiar with the Windows Registry skip to Step 9 onwards.

However, if you are well-versed in making registry adjustments, then you can proceed to step 7.
Step 7: Open the Registry Editor, to do so, tap Win + R and type in regedit and then press enter.
Step 8: Navigate to the following path:
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
Step 9: Delete any registry keys or sub-keys created by PayDay ransomware.
Step 10: Close the Registry Editor and empty the Recycle Bin.
Try to recover your encrypted files using their Shadow Volume copies
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if PayDay ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

To make sure that nothing is left behind and that the PayDay ransomware is completely removed, use the following antivirus program. To do so, refer to the instructions below.
Perform a full system scan using SpyRemover Pro. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOSscreen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Optionuse the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Boxwill show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading the program. Installation will start automatically once download is done.
- Click OK to launch it.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register the program to protect your computer from future threats.