What is Magniber ransomware? And how does it carry out its attack?
Magniber ransomware is a new ransomware infection which is being distributed by the Magnitude Exploit Kit and appears to be a new version of the Cerber ransomware. According to reports, Magiber ransomware’s first victims are from South Korea as well as some parts of Southeast Asia. It had gotten its name Magniber from the way it was facilitated using the Magnitude Exploit Kit.
The onset of the hacker campaign started when the cyber crooks loaded a newly devised malware into the Magnitude Exploit Kit. The same mechanism was used by Cerber ransomware strains. Security reports indicated that the captured strains are merely the first releases of the ransomware. One of the key characteristics of the Magnitude Exploit Kit is the fact that it is made specifically to infect users from South Korea and based on the reports, the email message is the preferred delivery mechanism.
Once the ransomware infects a computer, a number of attack sequences can be programmed. And depending on the configuration, it may feature different modules which can be activated or executed on the infected computer. Example of the modules includes Trojans, data theft and additional malware delivery. Magniber’s initial infiltration begins when it is copied to a temporary folder which can be changed according to the initial configuration. After Magniber’s files are changed with some random names, they are set for automatic startup when the infected PC boots.
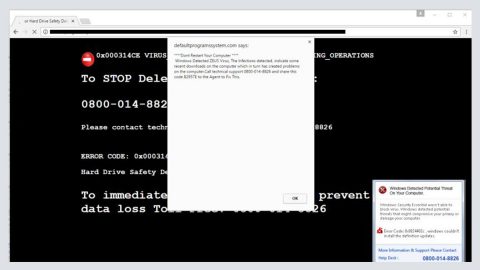
Magniber ransomware has lots of important characteristics – one of which is that it is able to spawn other malicious processes which are under its control. It can also interact with the child processes and inject some data on them. And one of the reasons why it is considered to be a dangerous threat is that some programs in the infected computer might be used to confuse users so that it can extract information from the users. For instance, an web browser which Magniber have messed with, if any sensitive information such as banking details, passwords, etc. is entered by the unsuspecting user, all the information will be recorded by the ransomware and sent to the crooks behind it. Moreover, this ransomware can also run shell commands all on its own, to make things worse, when it runs a shell command combined with some Trojan modules, it gives the cyber crooks nearly unlimited capabilities on using the victim’s computer remotely.
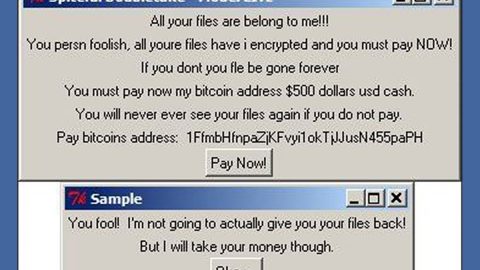
Magniber’s end goal is to blackmail users by using typical ransomware techniques. All the user’s files will be encrypted with a strong encryption algorithm security researchers were able to extract the bundled list of the captured strains and shows that Magniber targets files with the following extensions (these are just half of the extensions as the list is quite long):
doc, docx, xls, xlsx, ppt, pptx, pst, ost, msg, em, vsd, vsdx, csv, rtf, 123, wks, wk1, pdf, dwg, onetoc2, snt, docb, docm, dot, dotm, dotx, xlsm, xlsb, xlw, xlt, xlm, xlc, xltx, xltm, pptm, pot, pps, ppsm, ppsx, ppam, potx, potm, edb, hwp, 602, sxi, sti, sldx, sldm, vdi, vmx, gpg, aes, raw, cgm, nef, psd, ai, svg, djvu, sh, class, jar, java, rb, asp, php, jsp, brd, sch, dch, dip, p, vb, vbs, ps1, js, asm, h, pas, cpp, c, cs, suo, sln, ldf, mdf, ibd, myi, myd, frm, odb, dbf, db, mdb, accdb, sq, sqlitedb, sqlite3, asc, lay6, lay, mm, sxm, otg, odg, uop, std, sxd, otp, odp, wb2, slk, dif, stc, sxc, ots, ods, 3dm, max, 3ds, uot, stw, sxw, ott, odt, pem, p12, csr, crt, key, pfx, der, 1cd, cd, arw, jpe, eq, adp, odm, dbc, frx, db2, dbs, pds, pdt, dt, cf, cfu, mx, epf, kdbx, erf, vrp, grs, geo, st, pff, mft, efd, rib, ma, lwo, lws, m3d, mb, obj, x, x3d, c4d, fbx, dgn, 4db, 4d, 4mp, abs, adn, a3d, aft, ahd, alf, ask, awdb, azz, bdb, bib, bnd, bok, btr, cdb, ckp, clkw, cma, crd, dad, daf, db3, dbk, dbt, dbv, dbx, dcb, dct, dcx, dd, df1, dmo, dnc, dp1, dqy, dsk, dsn, dta, dtsx, dx, eco, ecx, emd, fcd, fic, fid, fi, fm5, fo, fp3, fp4, fp5, fp7, fpt, fzb, fzv, gdb, gwi, hdb, his, ib, idc, ihx, itdb, itw, jtx, kdb, lgc, maq, mdn, mdt, mrg, mud, mwb, s3m, ndf, ns2, ns3, ns4, nsf, nv2, nyf, oce, oqy, ora, orx, owc, owg, oyx, p96, p97, pan, pdb, pdm, phm, pnz, pth, pwa, qpx, qry, qvd, rctd, rdb, rpd, rsd, sbf, sdb, sdf, spq, sqb, stp, str, tcx, tdt, te, tmd, trm, udb, usr, v12, vdb, vpd, wdb, wmdb, xdb, xld, xlgc, zdb, zdc, cdr, cdr3, abw, act, aim, ans, apt, ase, aty, awp, awt, aww, bad, bbs, bdp, bdr, bean, bna, boc, btd, cnm, crw, cyi, dca, dgs, diz, dne, docz, dsv, dvi, dx, eio, eit, emlx, epp, err, etf, etx, euc, faq, fb2, fb, fcf, fdf, fdr, fds, fdt, fdx, fdxt, fes, fft, flr, fodt, gtp, frt, fwdn, fxc, gdoc, gio, gpn, gsd, gthr, gv, hbk, hht, hs, htc, hz, idx, ii, ipf, jis, joe, jp1, jrtf, kes, klg, knt, kon, kwd, lbt, lis, lit, lnt, lp2, lrc, lst, ltr, ltx, lue, luf, lwp, lyt, lyx, man, map, mbox, me, mel, min, mnt, mwp, nfo, njx, now, nzb, ocr, odo, of, oft, ort, p7s, pfs, pjt, prt, psw, pu, pvj, pvm, pwi, pwr, qd, rad, rft, ris, rng, rpt, rst, rt, rtd, rtx, run, rzk, rzn, saf, sam, scc, scm, sct, scw, sdm, sdoc, sdw, sgm, sig, sla, sls, smf, sms, ssa, sty, sub, sxg, tab, tdf, tex, text, thp, tlb, tm, tmv, tmx, tpc, tvj, u3d, u3i, unx, uof, upd, utf8, utxt, vct, vnt, vw, wbk, wcf, wgz, wn, wp, wp4, wp5, wp6, wp7, wpa, wpd, wp, wps, wpt, wpw, wri, wsc, wsd, wsh, wtx, xd, xlf, xps, xwp, xy3, xyp, xyw, ybk, ym, zabw, zw, abm, afx, agif, agp, aic, albm, apd, apm, apng, aps, apx, art, asw, bay, bm2, bmx, brk, brn, brt, bss, bti, c4, ca, cals, can, cd5, cdc, cdg, cimg, cin, cit, colz, cpc, cpd, cpg, cps, cpx, cr2, ct, dc2, dcr, dds, dgt, dib, djv, dm3, dmi, vue, dpx, wire, drz, dt2, dtw, dv, ecw, eip, exr, fa, fax, fpos, fpx, g3, gcdp, gfb, gfie, ggr
During the encryption, Magniber appends random extensions to the encrypted files such as .lhsdj or .kgpvwner. After it encrypts the targeted files, the ransomware communicates with the command and control server to report the encrypted files. The experts found that the ransomware does not target certain critical folders that may render the system unusable. These certain folders are as follows:
:\documents and settings\all users\
:\documents and settings\default user\
:\documents and settings\localservice\
:\documents and settings\networkservice\
\appdata\local\
\appdata\locallow\
\appdata\roaming\
\local settings\
\public\music\sample music\
\public\pictures\sample pictures\
\public\videos\sample videos\
\tor browser\
\$recycle.bin
\$windows.~bt
\$windows.~ws
\boot
\intel
\msocache
\perflogs
\program files (x86)
\program files
\programdata
\recovery
\recycled
\recycler
\system volume information
\windows.old
\windows10upgrade
\windows
\winnt
After the encryption, Magniber ransomware drops its ransom note named READ_ME_FOR_DECRYPT_[id].txt on each folder where there are encrypted files. The ransom note contains the following content:
ALL Y0UR D0CUMENTS, PHOTOS, DATABASES AND OTHER IMP0RTANT FILES HAVE BEEN ENCRYPTED! ====================================================================================================
“Your files are NOT damaged! Your files are modified only. This modification is reversible.
The only 1 way to decrypt your files is to receive the private key and decryption program.
Any attempts to restore your files with the third-party software will be fatal for your files! ====================================================================================================
To receive the private key and decryption program follow the instructions below:
- Download “Tor Browser” from https://www.torproject.org/ and install it.
- In the “Tor Browser” open your personal page here:
http://[victim_id].ofotqrmsrdc6c3rz.onion/EP866p5M93wDS513
Note! This page is available via “Tor Browser” only. ====================================================================================================
Also you can use temporary addresses on your personal page without using “Tor Browser”:
http://[victim_id].bankme.date/EP866p5M93wDS513
http://[victim_id].jobsnot.services/EP866p5M93wDS513
http://[victim_id].carefit.agency/EP866p5M93wDS513
http://[victim_id].hotdisk.world/EP866p5M93wDS513
Note! These are temporary addresses! They will be available for a limited amount of time!”
Follow the removal guide below to terminate Magniber ransomware from your computer.
Step1. Open the Task Manager by simply tapping Ctrl + Shift + Esc keys on your keyboard.
Step2. Under the Task Manager, go to the Processes tab and look for any suspicious-looking process which takes up most of your CPU’s resources and is most likely related to Magniber ransomware.

Step3. After that, close the Task Manager.
Step4. Tap Win + R, type in appwiz.cpl and click OK or tap Enter to open Control Panel’s list of installed programs.
Step5. Under the list of installed programs, look for Magniber ransowmare or anything similar and then uninstall it.

Step6. Next, close Control Panel and tap Win + E keys to launch File Explorer.
Step7. Navigate to the following locations below and look for Magniber ransomware’s malicious components such as READ_ME_FOR_DECRYPT_[id].txt as well as other suspicious files and then delete all of them.
- %TEMP%
- %WINDIR%\System32\Tasks
- %APPDATA%\Microsoft\Windows\Templates\
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
Step8. Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use PC Cleaner Pro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step9. Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step10. Navigate to the following path:
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
Step11. Delete the registry keys and sub-keys created by Magniber ransomware.
Step12. Close the Registry Editor and empty your Recycle Bin.
Try to recover your encrypted files using the Shadow Volume copies
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if Magniber ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

It is important to make sure that nothing is left behind and that Magniber ransomware is completely removed use the following antivirus program. To use it, refer to the instructions below.
Perform a full system scan using SpyRemover Pro. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOSscreen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Optionuse the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Boxwill show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading the program. Installation will start automatically once download is done.
- Click OK to launch it.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register the program to protect your computer from future threats.