What is Cezar ransomware? And how does it attack the targeted computer?

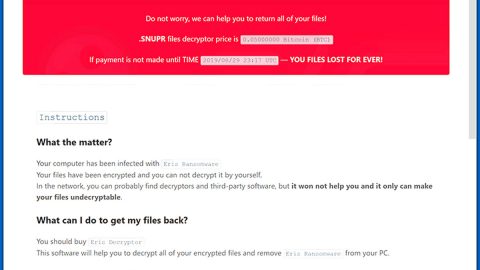
Cezar ransomware is a file-encrypting virus and a variant of the Dharma crypto-malware family. It has similarities with the Crysis ransomware with the way it was programmed. It could render your files useless by appending .cezar or .cesar file extensions. Followed by the completion of the data encryption, the virus drops its ransom note in a HELP.txt file that contains a short message:
To decrypt files, write to my email [email protected]
As you can see, it isn’t really clear how much the ransom money is, which could mean that the cyber crooks behind Cezar ransomware may be open to negotiations with its victims. Nevertheless, you shouldn’t think of reaching out to these crooks for they might only scare and urge you into paying the ransom and you might unknowingly grant them further access to your computer which could lead to more trouble.
In addition, Cezar ransomware might also add one of the following extensions to the encrypted files:
- .id-.[[email protected]].cesar;
- .id-.[[email protected]].cesar.
So if you’re one of the victims of Cezar ransomware, it is highly recommended that you use a decent anti spyware program just like SpyRemover Pro to remove the malware from your computer.
How does Cezar ransomware spread its infection?
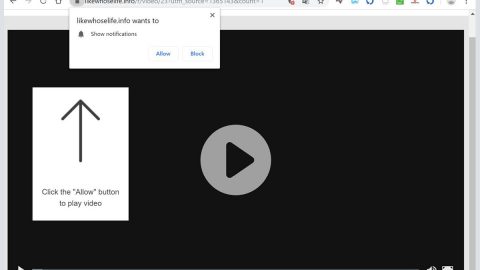
Cezar ransomware’s distribution method is quite unclear since its infections rate is not that high. But according to our specialists, its distribution technique should not differ from other malware which means that, just like most ransomware infections, Cezar’s malicious files are spread using spam email campaigns. It is one of the most popular ransomware distributions among this type of infection. Aside from that, it can also spread its infection on third party pages that presents themselves as P2P websites. These kinds of websites contain not just ransomware virus but also other kinds of computer parasites.
Follow the given guidelines below for the successful removal of Cezar rasnomware and for the recovery of the encrypted files.
Step 1: Open Windows Task Manager by pressing Ctrl + Shift + Esc at the same time.

Step 2: Go to both the Application and Processes tabs and look for any suspicious applications and processes and then kill them.

Step 3: Open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.

Step 4: Look for Cezar ransomware or any suspicious program and then uninstall it/them.

Step 5: Hold down Windows + E keys simultaneously to open File Explorer.
Step 6: Go to the directories listed below and look for the malicious file associated with Cezar ransomware and delete it.
- %LOCALAPPDATA%
- %USERPROFILE%\Local Settings\Application Data
- %WINDIR%\System32
- %TEMP%
- %USERPROFILE%\downloads
Step 7: Go to your desktop and look for the ransom note; HELP.txt, as well the malicious files created by Cezar ransomware.
The next step below is not recommended for you if you don’t know how to navigate the Registry Editor. Making registry changes can highly impact your computer. So it is highly advised to use PC Cleaner Pro instead to get rid of the entries that Cezar ransomware created. So if you are not familiar with the Windows Registry skip to Step 12 onwards.
However, if you are well-versed in making registry adjustments, then you can proceed to step 8.
Step 8: Open the Registry Editor, to do so, tap Win + R and type in regedit and then press enter.
Step 9: Navigate to the path below:
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run
Step 10: Delete all the Values created by the ransomware virus.
Step 11: Close the Registry Editor.
Step 12: Empty the Recycle Bin.
Step 14: Try to recover your encrypted files.
Note: Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if Cezar Ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.
Follow the continued advanced steps below to ensure the removal of the ransomware infection:
Perform a full system scan using SpyRemover Pro.
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the Safe Mode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in Cezar http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between Cezar and http. Click OK.
- A dialog box will be displayed by Internet Cezar. Click Run to begin downloading SpyRemover Pro. Installation will start automatically once download is done.
- Click OK to launch the program.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register SpyRemover Pro to protect your computer from future threats.