What is CyberDrill ransomware? And how does it execute its attack on the infected PC?
CyberDrill ransomware is an encryption Trojan which is based on the open source platform, HiddenTear. According to security experts, CyberDrill has been active since February 2017 but it wasn’t finished yet by that time and only in September 2017 was it able to finish its improved version. Like all other crypto-malware, CyberDrill aims to encrypt files in a computer and hold them hostage until a ransom is given.
Based on the reports, CyberDrill ransomware seems to target small and medium businesses specifically. Once it infiltrates your computer, CyberDrill connects to ransomuhahawhere.cyberdrillexercise.com website and 128.199.240.181:80 address to download malicious files in the computer. It then connects to its remote server to start its attack. During its attack, it scans the computer’s drives for the following file types to encrypt:
.3gp, .7z, .apk, .avi, .bmp, .cdr, .cer, .chm, .conf, .css, .csv, .dat, .db, .dbf, .djvu, .dbx, .docm, ,doc, .epub, .docx .fb2, .flv, .gif, .gz, .iso .ibooks, .jpeg, .jpg, .key, .mdb .md2, .mdf, .mht, .mobi .mhtm, .mkv, .mov, .mp3, .mp4, .mpg, .mpeg, .pict, .pdf, .pps, .pkg, .png, .ppt .pptx, .ppsx, .psd, .rar, .rtf, .scr, .swf, .sav, .tiff, .tif, .tbl, .torrent, .txt, .vsd, .wmv, .xls, .xlsx, .xps, .xml, .ckp, .zip, .java, .py, .asm, .c, .cpp, .cs, .js, .php, .dacpac, .rbw, .rb, .mrg, .dcx, .db3, .sql, .sqlite3, .sqlite, .sqlitedb, .psd, .psp, .pdb, .dxf, .dwg, .drw, .casb, .ccp, .cal, .cmx, .cr2.
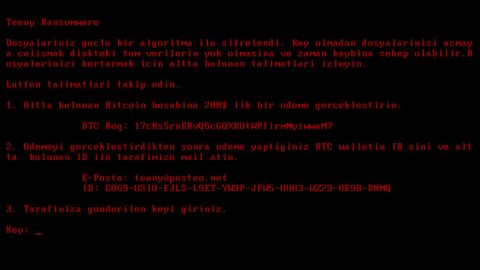
It encrypts all the file types given above using the AES encryption algorithm and then appends the .locked file extension on each one of them. After it finishes the encryption process, CyberDril drops a ransom note in the form of a text file named READ_IT.txt and opens a program window labeled as Cyberdrill_2 Ransomware. Both the program window and the text file contain the ransom note such as follows:
“Ooops, your files have been encrypted
Files have been encrypted with Cyberdrill_2 Ransomware and many Users will not be able to access sites host…
This is not a joke, Check sites now.
Sites will be DDoS-ed starting in 48 hours if you don’t pay only5 Bitcoins @ [RANDOM CHARACTERS]
If you don’t pay in next 24 hours, attack will start, yor service going down permanently.
price to stop increase to 1 BTC and will go up 1 BTC for every day of attack.
POur attacks are extremely powerful. o cheap protection will help.
Bitcoin is anonymous, nobody will ever know you cooperated”
Its ransom amount is approximately almost $20,000 which is insanely huge. Instead of paying the ransom, you can try out alternative ways to recover the encrypted files. And besides $20,000 is a lot, not to mention that you don’t get any assurances that you’ll really get your files back if you pay this obscene amount.
How does CyberDrill ransomware spread its infection?
CyberDrill ransomware spreads as an obfuscated file executable file named Ransomuhahawhere.exe file and because of its malicious executable file’s name, CyberDrill ransomware is also referred to as Ransommuhahawhere ransomware. Once its payload is executed, the ransomware then creates a folder named CyberDrill where it downloads the ransom note.
Follow the removal instructions below to terminate CyberDrill ransomware.
Step 1: Restart your PC into Safe Mode with Networking.
Windows XP/Windows 7
- Restart your PC.
- Tap F8 a couple of times while the BIOS screen is loading.
- Select Safe Mode with Networking by using the arrow keys on your keyboard.
- Tap Enter on your keyboard.
Windows 8 and Windows 8.1
- Move your mouse cursor to the lover-left corner of your screen and select the search icon.
- Type in PC Settings into the search box and select it.
- Click Update and recovery.
- Click Recovery and select Restart under the Advanced startup section.
- Click on Troubleshoot and select Advanced options.
- Click Startup Settings and select Restart.
- Tap the F5 key on your keyboard to select Safe Mode with Networking.
Windows 10
- Click the Windows button and choose Settings .
- Select Update & security and then click Recovery and choose Restart located under the Advanced startup section.
- Select Troubleshoot and click on Advanced options .
- Select Startup Settings click on Restart.
- Tap the F5 key on your keyboard to select Safe Mode with Networking.
Step 2: Tap Ctrl + Shift + Esc to pull up Windows Task Manager and look for CyberDrill ransomware’s malicious process and end it.

Step 3: Open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.

Step 4: Look for CyberDrill ransomware or any suspicious program and then Uninstall it/them.

Step 5: Tap Win + E keys to launch File Explorer.
Step 6: Navigate to the following locations below and look for CyberDrill ransomware’s malicious components such as READ_IT.txt and Ransomuhahawhere.exe then delete all of them.
- C:\Users\(your username)\Downloads
- C:\Users\(your username)\AppData\Local\Temp
- %TEMP%
- %APPDATA%
- %USERPROFILE%\Desktop
Step 7: Close the File Explorer. Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use PC Cleaner Pro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step 8: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 9: Navigate to the following path:
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
Step 10: Look for a registry value named My application and delete it.
Step 11: Close the Registry Editor and empty your Recycle Bin.
Try to recover your encrypted files using the Shadow Volume copies
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if CyberDrill ransomware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.

To make sure that nothing is left behind and that the CyberDrill is completely removed, use the following antivirus program. To use it, refer to the instructions below.
Perform a full system scan using SpyRemover Pro. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the Safe Mode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading the program. Installation will start automatically once download is done.
- Click OK to launch it.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register the program to protect your computer from future threats.