What is LockMe ransomware? And how does it execute its attack?
LockMe ransomware is a generic file-encoding malware that was first discovered on February 2, 2018. This ransomware threat has a geo-location service that allows its developers to keep track and monitor the infected computers. It seems to target both English and Russian-speaking users and is known to utilize spam bots to proliferate.
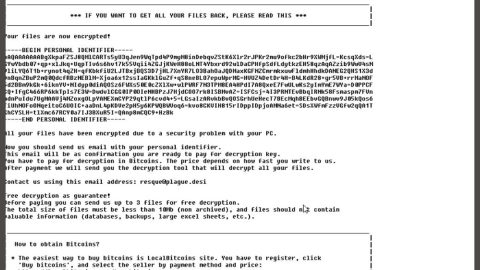
After it successfully infiltrates a targeted system, it scans the system for different kinds of files to encrypt like images, videos, audio, archives, databases, documents and other files used or opened frequently by users. It uses both the AES 256 and RSA 2048 encryption algorithm for encrypting files. Once it’s done with the encryption, it creates a file named “README_FOR_DECRYPT_YOUR_FILES.txt” which contains this message:
“All of your files have been Encrypted with military grade system and impossible to brute force, cracking, or reverse engineering it!
If you want all of your files back send me 0.03 BTC.
[+] Your Unique ID : [***] [+] Send BTC To This Address : 1LockMeEPLr4ZRsoht8Wp6idBsT5TuBXtX
[+] Send BTC : 0.03 BTC
[+] Contact Email :
[email protected] |
[email protected]
*) Don’t try to change the ‘.lockme’ extensions, if you change it, your all files can be broken and can’t be restored forever.
*) If you’ve made a payment contact
[email protected] |
[email protected].
*) If you did not make a payment all of your private files will be leaked on the internet (private photos, documents, videos, and more).
Question: How to buy Bitcoin?
Answer: You can buy Bitcoin at this Website: bitcoin.com, coinbase.com, cex.io, paxful.com, coinmama.com, etc.
[+] Your IP : [***] | Your ID : [***] [+]”
As you can see, its ransom note provides all the necessary details to acquaint its victims with the crypto-malware as well as the conditions it imposed so victims could recover the encrypted files. At the time of writing, victims are asked to pay 0.03 BTC which is around $230 and then contact the crooks through the given email address at Lock[email protected] or [email protected]. Contacting these crooks as well as paying the ransom is not recommended as it would only be a total waste of money and time. The best way to deal with this ransomware is by making its removal your topmost priority. Once you’ve managed to remove it, you can use whatever backup copy you have of the affected files until security experts are able to come up with a free decryptor.
How does LockMe ransomware proliferate?
LockMe ransomware is delivered to its victims through phishing emails and appears to have similarities with other ransomware threats like [email protected] ransomware and FriedEx ransomware. LockMe ransomware, according to security experts may be delivered as a document with macro scripts. This macro-enabled document is used in executing a command in the infected system to connect to a remote server and download and install LockMe ransomware.
Refer to the set of instructions provided below to get rid of LockMe ransomware from your PC.
Step 1: Tap Ctrl + Shift + Esc keys to launch the Task Manager.
Step 2: Go to Processes and look for LockMe ransomware’s malicious process, right click on it and select End Process or End Task.

Step 3: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.
Step 4: Look for dubious programs that might be related to LockMe ransomware and then Uninstall it/them.

Step 5: Tap Win + E to launch File Explorer.
Step 6: After opening File Explorer, navigate to the following locations below and look for LockMe ransomware’s malicious components such as README_FOR_DECRYPT_YOUR_FILES.txt and the macro-enabled document you have downloaded and remove them all.
- %TEMP%
- %APPDATA%
- %DESKTOP%
- %USERPROFILE%\Downloads
- C:\ProgramData\local\
Step 7: Close the File Explorer.
Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use PC Cleaner Pro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then, by all means, go on to the next steps.
Step 8: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 9: Navigate to the listed paths below and look for the registry keys and sub-keys created by LockMe ransomware.
- HKEY_CURRENT_USER\Control Panel\Desktop\
- HKEY_USERS\.DEFAULT\Control Panel\Desktop\
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Step 10: Delete the registry keys and sub-keys created by LockMe ransomware.
Step 11: Close the Registry Editor.
Step 12: Empty your Recycle Bin.
You have to ensure that LockMe ransomware is completely removed and that nothing is left behind, use the following antivirus program. Refer to the instructions below to use it.
Perform a full system scan using SpyRemover Pro. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading the program. The installation will start automatically once a download is done.
- Click OK to launch it.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register the program to protect your computer from future threats.