What is Bud ransomware? And how bad is it?
Bud is a ransomware-type infection that encrypts files and imitates the infamous WannaCry ransomware. Bud ransomware was first discovered on September 15, 2017. Bud ransomware is an encryption Trojan that targets Windows operating systems. It spreads as a macro-enabled document via spam emails. if opened, the macro-enabled document executes a command to connect to its Command and Control server to drop the malicious executable file of Bud ransomware.
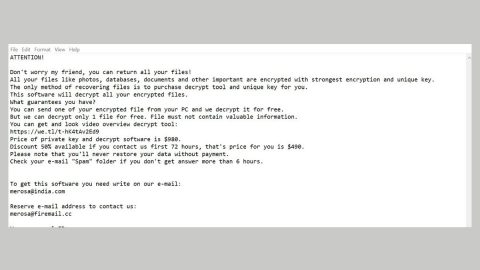
After the infiltration, it scans all the drives in the computer to look for files to target. Once it finds them, it starts the encryption and appends the .bud extension on each file. It then opens a pop-up window that contains the following ransom note:
Oooops, your important files are encrypted!
If you see this text, then your files are no longer accessible, because they have been encrypted. Perhaps you are busy looking for a way to recover your files. Nobody can recover your files without our decryption key. We guarantee that you can recover your files safely and easily. All you need to do is submit the payment to the BTC address down below. After the payment is sent, click the check – (payment button) and you get your files back. The fun start now, every hour more files will get lost forever, so hurry up!
Send 500 Euro to the bitcoin address:
1xyCdx4r6BNMfFXhraEeUqtyehZDBta1H
Based on its ransom note, the encrypted files can only be restored using a decryption key. It may be true since right now, there isn’t accurate information as to what is the encryption algorithm it used in encrypting the files. The decryption key offered by these crooks cost 500 Euro. No matter how desperate you get, paying the ransom isn’t a good idea. In fact it might only get you nowhere for there is no guarantee that these crooks will really give you the decryption key once payment is sent. The best thing you could do is to try to recover the encrypted files using your backups or recover them using their Shadow Volume copies.
How does it disseminate its infectious file?
As previously mentioned, Bud ransomware spreads as a macro-enabled document using that are attached to spam emails. These spam emails usually contains some catchy subject that may lure you into opening the message and even convince you to download the attachment. Once you download and open the attachment, that’s when the attack begins. So before you open any email messages, especially the ones from unknown senders, make sure that you double check them first and to scan all attachments you download using a reputable anti malware program like SpyRemover Pro.
To terminate Bud ransomware, make use of the following removal instructions.
Step 1: Reboot your computer into Safe Mode with Command Prompt by pressing F8 a couple of times until the Advanced Options menu appears.

Step 2: Navigate to Safe Mode with Command Prompt using the arrow keys on your keyboard. After selecting Safe Mode with Command Prompt, hit Enter.
Step 3: After loading the Command Prompt type cd restore and hit Enter.

Step 4: After cd restore, type in rstrui.exe and hit Enter.

Step 5: A new window will appear, and then click Next.

Step 6: Select any of the Restore Points on the list and click Next. This will restore your computer to its previous state before being infected with the Bud Ransomware.
Step 7: A dialog box will appear, and then click Next.

Step 8: After the system restore process; download SpyRemover Pro to remove any remaining files or residues of the Bud ransomware.
Step 9: Try to recover your encrypted files.
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if the crypto-malware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.
Follow the continued advanced steps below to ensure the removal of the Bud ransomware:
Perform a full system scan using SpyRemover Pro.
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the Safe Mode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Box will show up.
- Type in explorer http://www.fixmypcfree.com/install/pccleanerpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading PC Cleaner Pro. Installation will start automatically once download is done.
- Click OK to launch PC Cleaner Pro.
- Run PC Cleaner Pro and click the Click to Start Scan button to perform a full system scan.
- After all the infections are identified, click FIX ALL.