What is Matroska ransomware?
Matroska ransomware is a file-encrypting malware which is also known as HUSTONWEHAVEAPROBLEM ransomware. Matroska ransomware was first discovered way back in July 25, 2017. It was developed using the infamous HiddenTear open source platform which is commonly used by crooks to create ransomware infections. Cyber criminals take advantage of poorly protected Remote Desktop Protocol accounts. The malware may be installed on your computer directly by using your system’s vulnerabilities.
This ransomware seems to run as a malicious executable file named mscaut.exe, which is used to infect your computer. It then scans your computer for the following file types:
.txt, .doc, .docx, .xls, .xlsx, .pdf, .pps, .ppt, .pptx, .odt, .gif, .jpg, .png, .db, .csv, .sql, .mdb.sln.php, .asp, .aspx, .html, .xml, .psd, .frm, .myd, .myi, .dbf, .mp3, .mp4, .avi, .mov, .mpg, .rm, .wmv, .m4a, .mpa, .wav, .sav, .gam, .log, .ged, .msg, .myo, .tax, .ynab, .ifx, .ofx, .qfx, .qif, .qdf, .tax2013, .tax2014, .tax2015, .box, .ncf, .nsf, .ntf, .lwp
After it scans your computer for the file types stated above, it starts to encrypt them by appending the [email protected] to each file. Once the encryption is done, it displays a long ransom note which contains information about Matroska ransomware. Here’s the full context of the note:
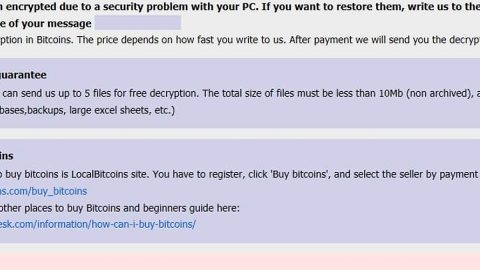
“YOUR FILES ARE ENCRYPTED!
Your personal ID
All your files have been encrypted due to a security problem with your PC.
To restore all your files, you need a decryption.
If you want to restore them, write us to t e e-mail
[email protected].
In a letter to send Your personal ID (see In the beginning of this document).
You have to pay for decryption in Bitcoins.
The price depends on how fast you write to us.
After payment we will send you the decryption tool that will decrypt all your files.
In the letter, you will receive instructions to decrypt your files!
In a response letter you will receive the address of Bitcoin-wallet, which is necessary to perform the transfer of funds.
HURRY! Your personal code for decryption stored with us only 72 HOURS!
Our tech support is available 24 \ 7
Do not delete: Your personal ID
Write on e-mail, we will help you!
Free decryption as guarantee
Before paying you can send to us up to 1 files for free decryption.
Please note that files must NOT contain valuable information and their total size must be less than 5Mb.
When the transfer is confirmed, you will receive interpreter files to your computer.
After start-interpreter program, all your files will be restored.
Attention!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
Do not attempt to remove the program or run the anti-virus tools
Attempts to self-decrypting files will result in the loss of your data
Decoders are not compatible with other users of your data, because each user’s unique encryption key”
The ransomware generates a personal ID number which, as you can see, is included in the ransom note. As per the ransom note, your files have been encrypted because of some security problem which isn’t true of course.
As of now, the cyber security groups all over cyber space haven’t come up with any decryptors or ways to decrypt the encrypted files. However, you can still try to recover them using the Windows Previous Version feature. After all, there’s no harm in trying.
How does this infection spread?
This malware spreads its infection by disseminating malicious spam emails that are sent to random email addresses. According to security experts, its malicious file is a Microsoft Word document which is macro-enabled. Once you open the email and download its attachment, the macro-enabled document will execute a command to connect to the malware’s Command and Control server. Once that happens, it will start its attack on your computer. And as pointed out earlier, this ransomware also spreads using unsecured Remote Desktop Protocols which allows users to connect and control a computer remotely.
To wipe out this dangerous ransomware infection, carefully follow the removal guidelines below.
Step 1: Open Windows Task Manager by pressing Ctrl + Shift + Esc at the same time.
Step 2: Go to the Processes tab and look for any suspicious processes and then kill them.
Step 3: Open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.
Step 4: Look for Matroska ransomware or any suspicious program and then Uninstall.
Step 5: Hold down Windows + E keys simultaneously to open File Explorer.
Step 6: Go to the following paths and look for the ransomware’s malicious executable file, mscaut.exe and delete it.
-
%USERPROFILE%\Downloads
-
%USERPROFILE%\Desktop
-
%TEMP%
Step 7: After that, go to the following paths and look for HOW_TO_RECOVER_ENCRYPTED_FILES.txt and delete it.
-
%ALLUSERSPROFILE%\Start Menu\Programs\Startup
-
%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup
Step 8: Since there are many ransom notes created, delete those as well.
Step 9: Empty the Recycle Bin.
Step 10: Try to recover your encrypted files.
Restoring your encrypted files using Windows’ Previous Versions feature will only be effective if the malware hasn’t deleted the shadow copies of your files. But still, this is one of the best and free methods there is, so it’s definitely worth a shot.
To restore the encrypted file, right-click on it and select Properties, a new window will pop-up, then proceed to Previous Versions. It will load the file’s previous version before it was modified. After it loads, select any of the previous versions displayed on the list like the one in the illustration below. And then click the Restore button.
Follow the continued advanced steps below to ensure the removal of the Matroska ransomware:
Perform a full system scan using SpyRemover Pro.
-
Turn on your computer. If it’s already on, you have to reboot it.
-
After that, the BIOS screen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
-
To navigate the Advanced Option use the arrow keys and select Safe Mode with Networking then hit Enter.
-
Windows will now load the Safe Mode with Networking.
-
Press and hold both R key and Windows key.
-
If done correctly, the Windows Run Box will show up.
-
Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
-
A dialog box will be displayed by Internet Explorer. Click Run to begin downloading SpyRemover Pro. Installation will start automatically once download is done.
-
Click OK to launch SpyRemover Pro.
-
Run SpyRemover Pro and perform a full system scan.
-
After all the infections are identified, click REMOVE ALL.
-
Register SpyRemover Pro to protect your computer from future threats.