What is Network Security Breach?
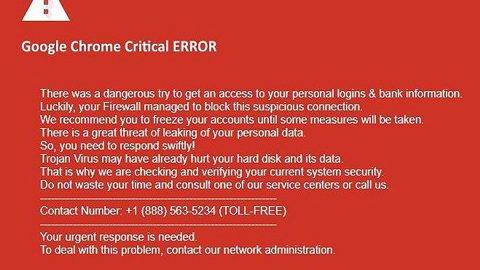
Network Security Breach is a new tech support scam roaming the web. It belongs to the Trojan group of tech support scams. Network Security Breach displays a fake Windows Update screen as you can see on the illustration above. The fake Windows Update screen is followed by an error message stating that your computer was deactivated because of a network security breach. You are then prompted to enter a product key to unlock your PC and to call the support number provided to call for help. Such tactics is only known to tech support scammers. Once it gets a hold of your computer, it prevents you access to your desktop or using any of your programs and displays the following error message:
“Configuring updates: Stage 2 of 3 – 10% complete.
Do not turn off your computer.”
Followed by:
“Microsoft Windows has detected some suspicious activities on this computer.
Due to have a Network Security Breach your Microsoft Windows got de-activated,
to activate please enter the product key.
Error Code: 0x00AEM001489
Invalid product key:
Computer Name:
Support: Call 1-866-324-2085”
Evidently, it is not advised calling the number provided for the cyber crooks behind the Network Security Breach tech support scam will only convince to pay for unnecessary service or urge you to pay and install a suspicious program which could potentially harm your PC.
It goes without saying that this tech support scam is pure hell bent on deceiving users as they reach the point of preventing users from accessing their computer unlike other browser-based tech support scam which randomly pops up on browsers while surfing the internet. You don’t have to panic when you see this seemingly alarming message disguising as some Windows error for it is only a means to extort money from users like you.
How does Network Security Breach proliferate online?
Just like all tech support scams, Network Security Breach scam proliferates online using the bundling technique. Take note that this Trojan is installed by other programs which did not adequately disclose that other programs will be installed along with it which is why it is very important to pay attention during the installation process especially when you’re installing a freeware or shareware you’ve obtained from free sharing sites. And when the installation screen shows you the Custom or Advanced option, it is recommended that you go over this setup so that you can discard the additional programs that were added in the installation package.
To wipe out Network Security Breach scam from your computer, refer to the following instructions.
Step 1: Unlock your screen by typing g6r-qrp6-h2 or yt-mq-6w as the product key into the unlock box.
Step 2: Open the Windows Task Manager by pressing Ctrl + Shift + Esc at the same time. Proceed to the Processes tab and look for suspicious processes that can be related to the Network Security Breach scam.

Step 3: Close the Task Manager and open Control Panel by pressing the Windows key + R, then type in appwiz.cpl and then click OK or press Enter.
Step 4: Look for Network Security Breach scam or any suspicious-looking program and then Uninstall it/them.

Step 5: Open the File Explorer by simply tapping Win + E keys.
Step 6: Navigate to the following locations below and look for Network Security Breach malicious components such suspicious files it created and then delete all of them.
- %TEMP%
- %APPDATA%
- %USERPROFILE%\Downloads
- %USERPROFILE%\Desktop
Step 7: Close the File Explorer. Before you proceed to the next steps below, make sure that you are tech savvy enough to the point where you know exactly how to use and navigate your computer’s Registry. Keep in mind that any changes you make will highly impact your computer. To save you the trouble and time, you can just use PC Cleaner Pro, this system tool is proven to be safe and excellent enough that hackers won’t be able to hack into it. But if you can manage Windows Registry well, then by all means go on to the next steps.
Step 8: Tap Win + R to open Run and then type in regedit in the field and tap enter to pull up Windows Registry.

Step 9: Navigate to the following path:
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
Step 10: Delete the registry keys and sub-keys created by Network Security Breach scam to prevent it from running again.
Step 11: Close the Registry Editor.
Step 12: Empty your Recycle Bin.
To make sure that nothing is left behind and that the Network Security Breach scam is completely removed, use the following antivirus program. To use it, refer to the instructions below.
Perform a full system scan using SpyRemover Pro. To do so, follow these steps:
- Turn on your computer. If it’s already on, you have to reboot
- After that, the BIOSscreen will be displayed, but if Windows pops up instead, reboot your computer and try again. Once you’re on the BIOS screen, repeat pressing F8, by doing so the Advanced Option shows up.
- To navigate the Advanced Optionuse the arrow keys and select Safe Mode with Networking then hit
- Windows will now load the SafeMode with Networking.
- Press and hold both R key and Windows key.
- If done correctly, the Windows Run Boxwill show up.
- Type in explorer http://www.fixmypcfree.com/install/spyremoverpro
A single space must be in between explorer and http. Click OK.
- A dialog box will be displayed by Internet Explorer. Click Run to begin downloading the program. Installation will start automatically once download is done.
- Click OK to launch it.
- Run SpyRemover Pro and perform a full system scan.
- After all the infections are identified, click REMOVE ALL.
- Register the program to protect your computer from future threats.